
That information can include checking and credit card account numbers, social security numbers, and other sensitive information. Tails always starts with a clean slate and any evidence of the activities you engage in while using Tails disappears when you shut down Tails. This includes evidence of any websites you visit, files you open, passwords you use, and even any other devices or networks you connect to. Tails never writes anything to the computer’s hard drive, running only from the RAM of the computer, which is wiped clean when the computer is shut down.
It’s Hard To Access: False

Dark web hosts project which ends with .onion (aka onion sites) and not .com, .net, .org, etc. that we generally operate with. And since normal browsers can’t browse such websites, you need something like the Tor browser to surf the dark web. The dark web is actually considered to be a small part of the deep web. It can only be accessed through special networks like Tor or via static IPs shared privately. Technical considerations here involve encryption strength; weak implementations undermine the very privacy this layer seeks to protect. The Deep Web thus balances safeguarding data with the practicalities of access, a dynamic critical to modern digital operations.
What Types Of Content Exist On The Deep Web?
- It was created in 1999 as a secure communication platform for people and groups working on liberatory social change.
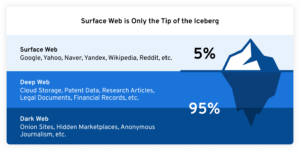
- Below the surface of the internet — whose web pages are indexed by popular search engines — exists something called the deep web, and further below that, the dark web.
- For those needing an additional layer of privacy, the Dark Web provides more anonymity.
- Although the deep web and the dark web may seem intimidating and dangerous, they’re actually surprisingly simple services to get started with and use.
This includes websites in the design stage and draft blogs in content management systems such as WordPress. Because the deep web is not fully-indexed with mainstream search engines, often the only way to find such sites is to know the exact internet address to use. There are some specialized websites or search engines that catalog some deep websites. For instance, academic resources on the deep web may be found using platforms like PubMed, LexisNexis, Web of Science, or Project MUSE.
What Kind Of Experience Do You Want To Share?
In Tor’s case, this is facilitated by routing encrypted traffic through layers of relays around the world. The deep web is essentially the unindexed portion of the web that search engines cannot access. The Darknet is a subset of the Internet operating over encrypted, anonymous overlay networks that require special software like Tor, Freenet, or I2P. In fact, it is likely some 500 times larger than the surface web and may contain as much as 96 percent of online content.
Uncovering Private Data In Secondhand Sales
The affiliates distribute the ransomware packages through the dark web. These attacks often include stealing victims’ data and threatening to release it on the dark web if the ransom isn’t paid. You could certainly go much deeper into the topic, but we hope the information provided here has given you a basic understanding of what the deep web/dark web are, how they function and why they exist. More importantly, you should now know how to access these hidden sectors of the internet at your leisure. We always recommend using a reliable VPN when accessing the deep web or dark web. That means that if your incoming traffic is routed through a node operated by cybercriminals, they can inject malware into the code of the response, without you ever knowing that it’s happened.
More On How To Stay Safe On The Dark Web
A private network, tagged as the deep web, can be right next to your house. It’s just the internet that isn’t within reach of standard search engine crawlers. For instance, the network maintained by some paid streaming service. Obviously, the search engines won’t be opting for a monthly subscription to index the catalog of such websites. “The Dark Web” is an overused term that can be a source of mystery and confusion for most cybersecurity professionals. Put simply, the Dark Web is any site, messaging platform, community, or other online entity that is not indexed by any search engine.
The Hidden Wiki & Co
To access the Freenet-based dark web, you need to install the Freenet application. If you have a legitimate or viable need to access the dark web, you’ll want to make sure you stay safe if you decide to use it. Some alleged services like the professional “hitmen” may just be scams designed to profit from willing customers. Reports have suggested the dark web offers many illegal services, from paid assassinations to trafficking for sex and weapons.
- Since this turmoil, management and oversight of the software powering the largest dark web network has been fairly stable and consistent.
- Significantly smaller than the tiny surface web, the dark web is considered a part of the deep web.
- In addition, encrypted messaging platforms like Telegram and QQ provide a safe haven for communications about malicious acts and are, therefore, popular among threat actors.
- However, it is reasonable to know your content and ensure proper authorization.
Certain details of your traffic can be intercepted at the entry and exit points of the node, by the people running those nodes, if they know what they’re doing and what they’re looking for. You’re also open to threats like end-to-end correlation attacks, so while Tor is a lot more secure and private, it’s by no means completely safe. The deep web is the part of the internet that constantly runs behind the scenes to protect all the private data people share and store.
The Main Differences Between The Dark Web & The Deep Web
A network browser gives you access to sites with the ‘.onion’ registry operator. Initially, the dark web was mainly used by government agencies, big businesses, hackers, and cybercriminals. However, technological advancements such as encryption and privacy-focused browsers like Tor enabled the general public to access it. One option is to try DuckDuckGo’s .onion version, which is great for privacy.
Legal Vs Illegal Activities

Formerly, Darren served on the Committee of Technology Infrastructure under Mayor Richard Daley. Even completing a transaction is no guarantee that the goods will arrive. Many need to cross international borders, and customs officials are cracking down on suspicious packages. The dark web news site Deep.Dot.Web teems with stories of buyers who have been arrested or jailed for attempted purchases. The dark web has flourished thanks to bitcoin, the crypto-currency that enables two parties to conduct a trusted transaction without knowing each other’s identity.
The person or group who has posted a webpage on the open web doesn’t care who has access to it or what can be done with it. To use a real-world example, you probably don’t care who in a large group knows your name or the color of your hair. Keep reading to discover the differences between the deep web and dark web and what they mean for your online safety. Funnily enough, they still own those traditional big channels of communication and there are still plenty of people following the same orientation as them.
Best Dark Web Sites 2025 – Detailed List
Virtually anything you can buy on the surface or clear web you can also find on the dark web. Books, video games, apparel and rare collectibles are some of the legal items you can buy on dark web commerce sites. You can never be sure of the motive of the person operating the node that your traffic is routed through. So hey, we’ve beaten around the bush quite a bit, let’s finally get you what you came here for, here’s how to access the deep web.


