An anonymous dark web user had logged on to a site called Camorra Hitman and made a...
To reinforce your privacy while on the dark web, consider adding on a VPN like Windscribe as...
In addition, the marketplace’s automatic photo metadata-stripping tool was bugged, allowing police to collect geolocation data for...
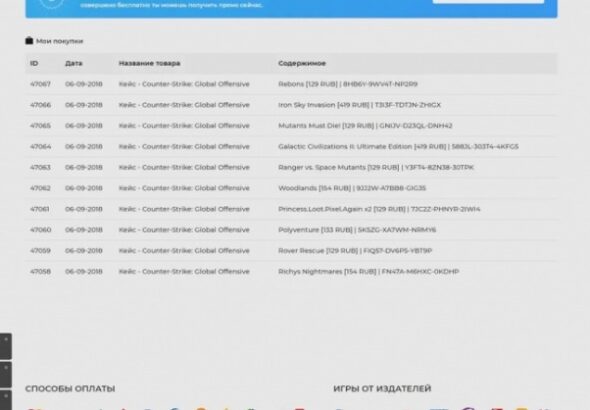
Research shows they build customer satisfaction through selling Indeed, marketing strategies used on the darknet look remarkably...
If you just want to check out their offers and prices, you can instantly view all the...
Senior project managers are in charge of setting deadlines, assembling construction teams, and organizing planning meetings. They...
Search engines like Google and Bing are our go-to tools for finding information quickly and easily. By...
Enjoy the taste of Heineken without ever leaving your house with the Heineken Express link. This is...
Even in the construction industry, conferences are an excellent way to learn from industry leaders and innovators....
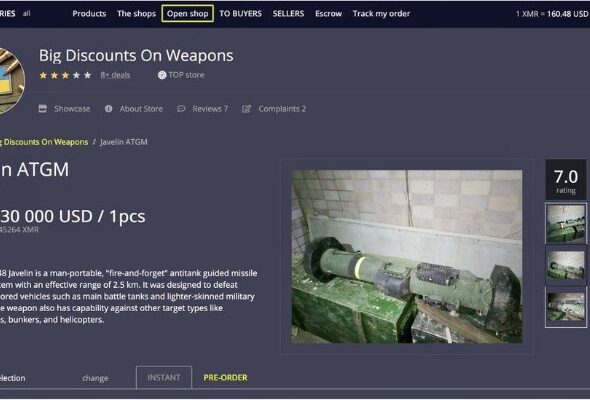
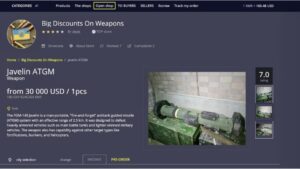
A darknet marketplace claiming to be affiliated with CJNG discovered by DarkOwl analysts offers drugs for sale....