
It is a platform that compiles a massive collection of malware samples, research articles, and threat analyses—making it a key resource for researchers and hacking enthusiasts. Despite all of this, Telegram is just one piece of the broader Dark Web ecosystem. Malicious actors use multiple platforms to coordinate, sell information, and launch cyberattacks. That’s why companies and organizations must remain vigilant about these underground networks, as a data breach or financial fraud can begin with a simple conversation on Telegram.
Top 6 Dark Web Telegram Groups And Channels In The UK

This emphasis on technical support is crucial for users who engage in credential theft.In Copyright Media channels, questions often revolve around finding more content from specific creators or resolving issues with media sharing restrictions. Users ask questions to clarify how to use specific software or resolve issues, much like in Credential Compromise channels. This reflects a need for guidance to effectively use pirated software and troubleshoot any problems that arise. The battle against piracy and the protection of copyright have become pivotal issues in the digital era. On one hand, digital technologies have enabled widespread copyright infringement; on the other, they have facilitated the proliferation of new creative works on a massive scale (Aguiar et al., 2024; Waldfogel, 2017; Wu and Zhu, 2022).
- These channels serve as underground marketplaces for various illegal activities, including the distribution of stolen credentials.
- Moon Cloud is a clear example of how cybercriminals have turned Telegram into a hub for the trade of stolen data.
- NoName057(16) is a clear example of how Telegram continues to serve as a critical tool for hacktivist groups and politically motivated cyber operations, leveraging the platform’s anonymity and ease of communication.
- While the dark web operates in the shadows, Telegram’s channels and groups are visible to a larger audience.
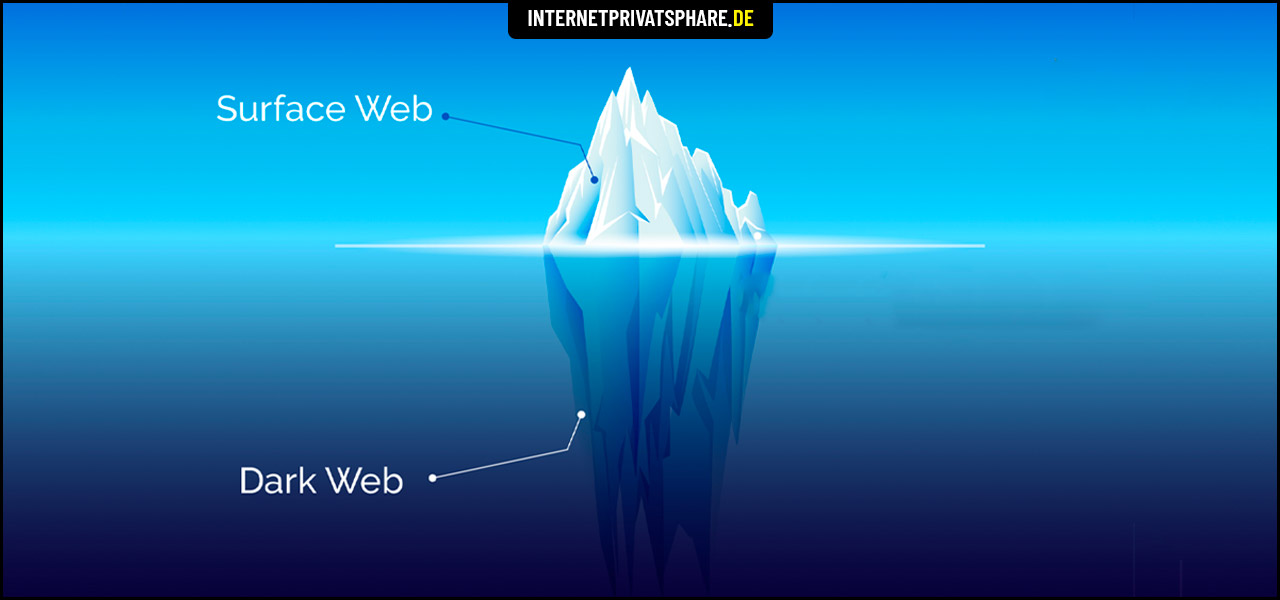
- When comparing dark web forums to illicit Telegram groups, it is important to consider the different levels of privacy each offers its users.
These sites act as a network for career cybercriminals to connect with potential collaborators. For example, they are used by Initial Access Brokers to auction access to organization’s infrastructure and by Ransomware-as-a-Service (RaaS) operators as a PR channel. In short, it is a space where stolen databases, leaked credentials, and exploited vulnerabilities are collected and shared, becoming a key reference point for those who closely monitor the world of cybercrime and cybersecurity. Moon Cloud is a clear example of how cybercriminals have turned Telegram into a hub for the trade of stolen data. This poses a serious risk to both individuals and organizations, as such credentials can be used in account takeovers, financial fraud, and unauthorized system access.
Real Cases Of Corporate Data Leaks On Telegram
There is an active demand for OTP bots, as many of these results displayed activity within minutes of the query. Generally, malicious actors purchase access to bank account login credentials first, then search for OTP bot availability in fraud-oriented Telegram channels. In the hands of a threat actor, these credentials can be abused to cause horrendous data breaches for individuals and organizations.
Standard Digital
Monitoring these forums not only helps identify potential threats but also provides actionable intelligence for investigating and dismantling criminal networks. Consequently, this aids in preventing various illegal activities, including drug trafficking, identity theft, and online fraud. Hacker groups, underground markets, and ransomware networks began using Telegram to distribute stolen data, sell hacking tools, and coordinate illicit operations.
Thirsty Data Centres Boom In Drought-hit Mexico

Illicit Telegram channels are a common new vector that facilitates the routine distribution of stolen credentials. In some cases this may be for free and in other cases the credentials may be purchased through automated mechanisms on specific channels. Cybercriminals doubt just how much anonymity they get when using dark web forums that administrators can easily monitor. While IP addresses and geolocations get hidden automatically through a special type of routing, there is the fear of being monitored by admins and having identities revealed.
Infected Devices And Illicit Telegram Channels

Additionally, 16 posts included ”proofs” such as screenshots or videos demonstrating successful logins or transactions, serving as evidence of the authenticity of the leaked credentials. Telegram is a popular messaging app, known for its secure and encrypted communication features. However, no platform is completely immune to threats, and Telegram users should be aware of common threats that can potentially compromise their privacy and security. In this article, we will explore some of these common threats, including phishing attacks, malware dissemination, social engineering, and fake accounts. By being aware of these threats, users can take necessary precautions to protect themselves and their sensitive information while using Telegram. Another important factor is how Telegram offers hacking groups and lone wolf actors a way of hardening their operations.
- Now based in Dubai, Telegram was started in 2013 by Russian brothers Pavel and Nicolai Durov and now has 700 million active monthly users.
- We found that 5 channels were dedicated to a single TV show, posting episodes in a sequential format.
- A new study has shed light on the world of Telegram’s darknet groups, showing Russian is the most dominant language across these groups on the popular messaging app, followed by English.
- Requests like ”Send on my page here in Telagram please” show a transactional nature, where users expect engagement in return for participation.
- Monitoring these forums not only helps identify potential threats but also provides actionable intelligence for investigating and dismantling criminal networks.
Currently, the channel claims to have a database of over 2 billion records available via a subscription-based model, making it one of the most active sources for buying and selling stolen credentials. Since its creation in 2019, vx-underground has gained recognition for hosting one of the largest online malware repositories. Its activity isn’t limited to Telegram—they also operate on Twitter and their official website, where they share information about new security breaches, malware trends, and verified threat reports. However, with millions of Telegram users posting terabytes of content each day, moderation is a herculean process. Through one-time password bots (OTP bots), threat actors can try to collect 2FA codes from victims at scale. When we conducted a search in 2022 on Telegram for the terms “OTP Bot” and “2FA Bot,” we found 1,700 results.
Search Darknet
Analysts noted that Telegram enabled a shift toward decentralised “broker networks,” where smaller groups coordinated sales of Genesis-style data. This decentralised model makes it far more challenging to target with a single operation. Established in April 2019 as a Russian-language group, EMP/mailpass/sqli Chat has since expanded into a global cybercrime discussion channel. With 5,695 members, the group remains active, serving as a hub for discussions on data breaches, compromised credentials, and underground trading. This channel provides real-time updates on detected credit card data, with some posts visibly displaying card numbers and other financial details. BidenCash claims to impose fines or bans on suppliers whose listings are repeatedly found in public sources.
On Telegram drug buyers and sellers chat on invite-only “channels”, some of which can have tens of thousands of active members, where anything from mescaline and “pink cocaine” to mephedrone and steroids, is available to buy. As with the dark web, there is always the risk of being scammed, although the reliability of individual sellers and their drugs are rated, reviewed and discussed. Among its users are those carrying out so-called “pig butchering” schemes, where victims are convinced to invest in a fake crypto platform and are tricked into believing they’re getting massive returns when really they’re losing money, Elliptic said. These include ransomware as a service vendors, stealer logs, marketplaces, credential dumps and hacking forums. Narcotics Express is a closed Telegram group, meaning users must request access to view content. However, once they are accepted, these users can trade and purchase illicit drugs, including cocaine, MDMA, and methamphetamines.
State Bank Of India (SBI) Employee Data Leak
Encryption is an interesting topic when it comes to illicit cybercriminal activity. Telegram offers end-to-end encryption for messages by default, which helps to avoid potential man-in-the-middle attacks that can snoop on messages in transit. Dark web forums and marketplaces also have an encryption option but threat actors need to use something like Pretty Good Privacy (PGP) to ensure encryption, which is less convenient. Any such services that were sought by a user in one of these malicious communities were often directed to navigate from Telegram to a dark web forum directly.

However, it is important to note that Telegram has been cracking down on illicit communities, making it less favorable for trading cyberattack methods. The platform actively removes channels and groups that engage in such activities, making it difficult for users to find these services. In July 2023, hackers used Telegram’s @sbi_data channel to expose the personal information of over 12,000 SBI employees, including names, addresses, contact numbers, PAN numbers, and photo IDs. The hackers posted stolen sensitive data on the platform, claiming to have exploited the company’s weak cybersecurity.



