These channels make the market more agile, allowing it to shift operations and communicate alerts whenever law enforcement actions are detected. Bitcoin and Monero are the main payment options, reflecting the market’s emphasis on anonymity and decentralized commerce. JCODE and Europol’s European Cybercrime Centre (EC3) continue to compile intelligence packages to identify entities of interest. Parsarad was also indicted by a federal grand jury in the Northern District of Ohio on drug trafficking charges related to the illegal business he ran on the dark web.

The other emerging issue is that current policing efforts treat dark web markets as the core threat, which might miss the wider landscape of digital harms. Illicit drug sales, for example, are promoted on social media, where platform features such as recommendation systems are affording new means of illicit drug supply. We’ve built a reputation for being one of the most trusted sites in this space. Tor mirrors for top markets, forums, and vendors are listed, giving you peace of mind. Our goal has always been simple—track reliable, official mirrors of popular dark web markets, and update users when something changes. By considering these factors, we aim to provide you with a comprehensive and reliable overview of the top darknet markets, empowering you to make informed decisions and prioritize your safety and security.
Fragmentation Of Ransomware Groups
One of the most notorious Dark Web incidents occurred in October 2013, when the FBI shut down Silk Road, the then-largest Dark Web marketplace. Founded by Ross William Ulbricht in 2011, Silk Road quickly established itself as the go-to destination for illegal items, particularly illegal drugs. When the FBI arrested Ulbricht in 2013 for money laundering and drug trafficking, among other offenses, the criminal complaint revealed the marketplace had generated over $1.2 billion in just two years. Short for “The Onion Router,” Tor uses the decentralized onion routing network to allow users to browse the internet anonymously.
Torrez Market
Cryptor developers are introducing novel techniques to evade detection by security solutions, incorporating these advances into their malware offerings. District Judge David O. Carter called this case “the most sophisticated fentanyl distribution ring that this court has seen.” “We will continue to monitor, investigate and bring to justice those who misuse the internet in a quest for profits with reckless disregard for the risk to public health and safety.” “This historic international seizure of firearms, deadly drugs, and illegal funds will save lives,” said Attorney General Pam Bondi.
Gift Cards

Chainalysis also noted that some markets are openly advertising their wares in Russia, with giant 3D billboards (Kraken Market) and QR codes on subway trains (Mega Darknet Market). Use Tor Browser from torproject.org for safe onion routing—update regularly. Latest updates from the darknet trading world as of February 2025—key shifts and developments. These shifts tie into how markets like these are evolving—check them out below.
High-volume vendors launch standalone shops using Tor and Monero, reducing dependency on marketplaces. These markets rely on encryption, escrow systems, and vendor ratings to function in a trustless environment. By consistently applying these straightforward security tips, you can significantly mitigate risks and better protect your privacy, finances, and legal standing when interacting with dark-web marketplaces. Infostealers and drainers will likely be increasingly promoted as subscription-based services, with traffers aiding in their distribution via scam pages and phishing schemes. Following stricter bans on Telegram channels hosting cybercriminals, experts predict a resurgence of activity on dark web forums.
- This website is made public with the intention to aid the Internet users with navigation of the so called dark web.
- However, you can trace its roots to the development of technologies like the Tor network or Freenet.
- Cloud platforms and IT services often store and process corporate data from multiple organizations, so a breach at just one company can open the door to many others.
- There’s also a privacy angle—some users live in countries with censorship or surveillance, and the dark web gives them a space to communicate or access information more freely.
- This fusion of AI with illicit marketplaces could open the door to new forms of large-scale fraud, intensifying the cat-and-mouse game between cybercriminals and law enforcement.
Tripping Drugs: Which Combinations Create Powerful Experiences?
- Activities on dark-web marketplaces are closely monitored by international law enforcement agencies.
- Darknet markets continue to evolve in 2025, adapting to law enforcement crackdowns and shifting user demands.
- Between January 2019 and September 2023, the majority of those queries came from underdeveloped countries with well-documented instances of internet censorship.
- It leverages a reputation-based vendor ranking system, where top sellers gain priority listings.
With tricks like ring signatures and stealth addresses, it keeps your transactions off the radar—unlike Bitcoin, which can leave a trail if you’re not careful. Incoming crypto volumes to Chinese drug precursor manufacturers have seen a significant decline, from USD 27.6 million in 2023 to USD 17.0 million in 2024. This drop may be driven in part by stronger actions from the Chinese government following the Biden-Xi summit of November 2023.
Users must look for platforms employing robust encryption protocols, secure escrow services, and advanced anti-phishing measures. Additional layers, such as two-factor authentication (2FA), encrypted PGP messaging, and built-in wallet security, significantly enhance protection against theft and hacking. Dark-web marketplaces operate through encrypted networks, primarily utilizing anonymity-enhancing technologies such as Tor (The Onion Router) and I2P (Invisible Internet Project).
Frequently Asked Questions (FAQs) About Dark Web Marketplaces
In addition to Wednesday’s arrests, agents served multiple federal search warrants and found evidence to include large amounts of cash, distribution amounts of suspected drugs. The defendants fulfilled drug orders through the various vendor accounts by packaging the drugs into parcels and by delivering those parcels to post offices and mailboxes in Los Angeles County and elsewhere. Avalyan is charged with one count of distribution of cocaine, one count of distribution of MDMA, and one count of distribution of distribution of methamphetamine. Gevorgyan is charged with one count of possession with intent to distribute MDMA and one count of possession with intent to distribute ketamine. Grigoryan is charged with one count of possession with intent to distribute methamphetamine. Nersesyan is charged with three counts of possession with intent to distribute methamphetamine, one count of possession with intent to distribute cocaine, and one count of possession with intent to distribute MDMA.
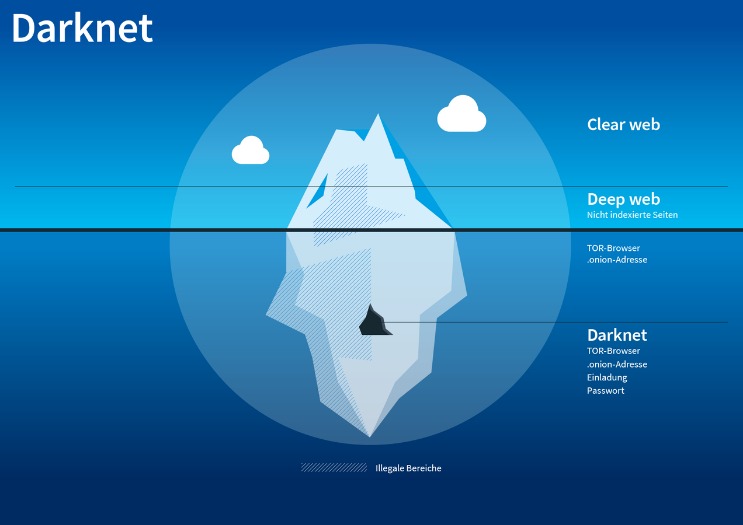
Missing The Wider Landscape Of Digital Harms
Dark web users rely on a combination of tools and networks to maintain their anonymity. Tor (The Onion Router) remains the most popular, routing data through multiple encrypted layers to hide users’ real IP addresses. Some individuals and groups also leverage I2P, a peer-to-peer network designed for continuous routing within a decentralized environment. Beyond these specialized networks, users often connect through VPN services and proxy chains to further mask their physical locations. Some dark web marketplaces even host content that’s not just illegal but extremely harmful, so it’s really important to understand the risks before diving in.
Compared to its predecessors, Archetyp enforced enhanced security expectations from its users. These included an advanced encryption program known as “Pretty Good Privacy” and a cryptocurrency called Monero. Unlike Bitcoin, which records every payment on a public ledger, Monero conceals all transaction details by default which makes them nearly impossible to trace.
Going forward, these trends—enhanced anonymity, specialized marketplaces, and increasingly sophisticated fraud—are likely to define the dark web’s trajectory. Cybersecurity professionals and investigators will need to employ equally advanced tools and collaborative strategies to keep pace with the rapidly shifting landscape. A crucial aspect of this work is blockchain analysis, where investigators track the movement of Bitcoin, Monero, and other cryptocurrencies through public and private ledgers. Advanced software tools help detect unusual transaction patterns, identify known “mixers,” and link wallet addresses to real-world identities. Meanwhile, deanonymizing technologies range from exploiting zero-day vulnerabilities in Tor or I2P to intercepting network traffic through compromised nodes. Coupled with big data analytics, these methods enable law enforcement to piece together small fragments of information, ultimately revealing a broader picture of criminal activity.
Cyber-Attacks And Scams
Darknet marketplaces face numerous challenges that can lead to their shutdown. Law enforcement raids represent one of the most common causes, as coordinated international operations often target servers, seize assets, and arrest site operators. Hacks and data breaches also threaten a marketplace’s stability; when user information is compromised or administrators lose control of critical infrastructure, many platforms collapse under the resulting mistrust. Finally, an “exit scam” can occur when marketplace operators abruptly shut down the site, absconding with user funds held in escrow, leaving buyers and vendors at a loss. With more than 40,000 listings and an estimated valuation of around USD 15 million, it features a broad array of illicit products, from narcotics and cybercrime tools to forged documents.