Buyers simultaneously active on multiple markets also play the role of connectors in the ecosystem. Therefore, we analyse the temporal network where nodes are the active markets and an edge between the nodes represents the number of multibuyers between them, what we henceforth call the multibuyer network. The structural change seen in the multiseller network is not observed in the multibuyer network, as show in Fig.
Best Free Firewall Software In 2025
In many ways, crypto has continued to gain mainstream acceptance, following the approval of spot Bitcoin and Ethereum exchange-traded products (ETPs) in the United States and revisions to the U.S. Financial Accounting Standards Board (FASB)’s fair accounting rules. Furthermore, inflows to legitimate services year-to-date (YTD) are the highest they’ve been since 2021, the previous bull market peak. In fact, aggregate illicit activity YTD fell by 19.6%, dropping from $20.9B to $16.7B, demonstrating that legitimate activity is growing more quickly than illicit activity on-chain. This encouraging sign points to the continued adoption of crypto globally. Among the most prominent threats on the darknet, KELA observed leaks and sales of Japanese entities’ data.
How To Protect Your Personal Data Online
It is assessed that only a minority have used it personally (see “Darknet Use in Southeast Asia” in Appendices). Even on the news, the Darkweb is generally not discussed in any great detail, with most stories relating to the arrest of cybercriminals who have used the Darkweb in some way. Markets overwhelmingly use XMR to avoid traceable Bitcoin transactions. Monero’s ring signatures, stealth addresses, and RingCT obfuscate transaction details—enhancing privacy and hindering traceability The Rise of Monero.
Vendors on Hydra also offered services such as “Hacking for Hire,” “Ransomware as a Service” (“RaaS”), and a myriad of money laundering features. Though the drug transactions were limited to Russia and its geographic neighbors, the cyber and money laundering tools were available to anyone in the world willing to pay. Conversely, transaction networks obtained from the blockchain contain the entire transaction data of the DWMs and U2U transactions, allowing a thorough investigation of the ecosystem as a whole. In fact, previous studies on DWM transaction networks have revealed crucial aspects of the ecosystem13,14,15. However, they have so far mainly focused on DWM users, without distinguishing between buyers and sellers, and neglecting the different weight that more active users may have in the system.

Marketplaces that maintain strict moderation policies—banning excessively harmful or exploitative products—also gain popularity among more ethically minded users. Users must look for platforms employing robust encryption protocols, secure escrow services, and advanced anti-phishing measures. Additional layers, such as two-factor authentication (2FA), encrypted PGP messaging, and built-in wallet security, significantly enhance protection against theft and hacking. Some fake sellers take your crypto and never ship what you ordered, or phishing sites that look like real marketplaces but steal your login info. And then there’s malware—click the wrong link or download the wrong file, and your device could get infected. Some are looking for illegal stuff they can’t buy elsewhere, like drugs or counterfeit documents.

Criminal Hacking Services
With tricks like ring signatures and stealth addresses, it keeps your transactions off the radar—unlike Bitcoin, which can leave a trail if you’re not careful. Most markets, like Abacus or Archetyp, love it for that privacy kick. Darknet markets trace their origins to the early 2000s, with the advent of Tor in 2002 by the U.S.
Escrow Surge
Word is, they’re pushing digital goods big-time next year—think stolen logins and cracked software. Alright, let’s get into the meat of it—the darknet markets that are ruling 2025. I’ve been poking around these places for a while now, from the giants like Abacus to the old-timers like Vice City. This isn’t just a quick list; it’s the full scoop on what they offer, how they keep things tight, and why they’re worth your time—or not. Whether you’re new to the dark web or a vet who’s seen it all, you’ll find something here to chew on.
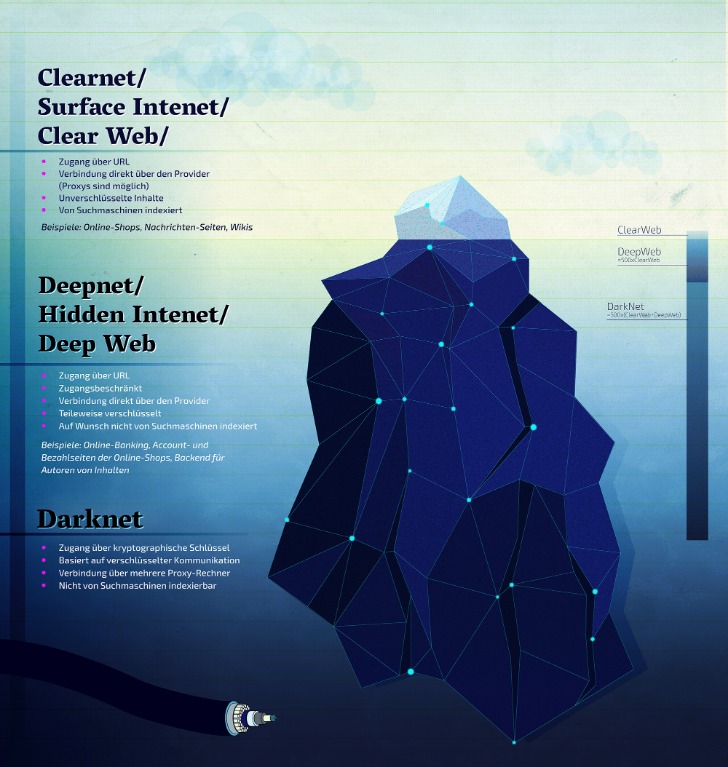
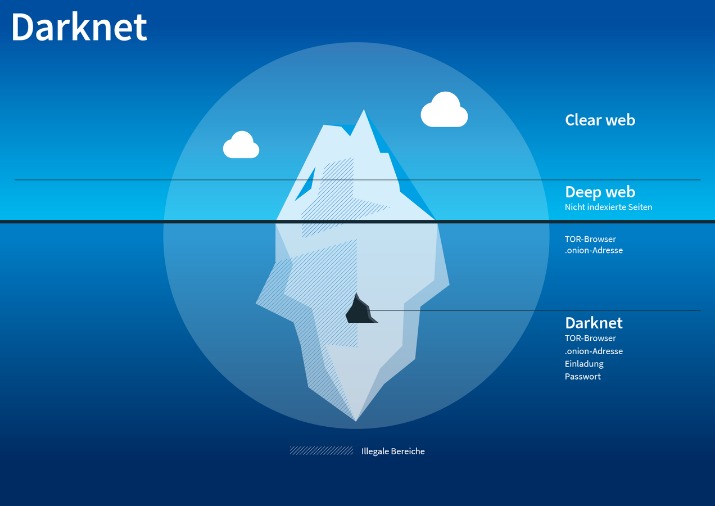
Introduction: How Much Of The Internet Can You See?
- Privacy-focused operators are shifting to Monero due to its default anonymity, compared to Bitcoin’s transparent ledger Darknet markets see BTC inflow drop to $2B.
- Markets overwhelmingly use XMR to avoid traceable Bitcoin transactions.
- In general, by understanding the operation of key players within the DWM ecosystem, our work highlights how appropriate strategies can be designed to counteract the online trade of illicit goods more effectively.
- During 2016 and 2017, AphaBay becomes the dominant market (see Fig. 3), polarizing sellers around its own ecosystem, such that the fraction of multisellers decreases to 10% of all sellers until its closure.
- The Silk Road was the first popular DNM which appeared on the scene in back in 2011.
- Dark markets continually adapt and evolve to stay ahead of law enforcement and security measures.
So, you need to be extremely cautious because the fake sites are often very similar to the real ones, making them dangerously convincing. Once you unknowingly install the spyware or ransomware, they can steal your identity or even hijack your crypto wallet. Too-good-to-be-true investment offers are another classic scam on the dark web.

THERE IS A PAUCITY OF RELIABLE DATA REGARDING DARKNET-ENABLED CRIME IN SOUTHEAST ASIA
Having JavaScript enabled on the dark web can cause havoc because it can reveal your IP address to your website. Also, previously, the Tor browser was vulnerable to JavaScript attacks as it provided hackers a pathway to track your activities by using the session details. Therefore, for security reasons, disable JavaScript on the Tor browser and enjoy an anonymous browsing experience on the dark net. It doesn’t use JavaScript, meaning the website won’t track your activities or exploit vulnerabilities. The website allows a personalized searching experience, where you can search according to your geographical location, country-specific, and keyword or price-specific search results. Look for ratings below 90% or no escrow—common red flags on markets like Torrez.
Range Of Available Products
Throughout the whole period of observation, the dominant category of buyers is market-U2U buyers followed by market-only buyers, representing on average 52% and 42% of all buyers, respectively. The U2U-only category is comparatively small, representing only 6% of all buyers on average. The number of market-U2U and market-only buyers also drops as a consequence of operation Bayonet. However, compared to sellers, the drop is notably smaller, and the number of buyers rapidly recovers to previous values. Moreover, the number of multibuyers increases, which suggests a fast response from buyers to external shocks by trying to diversify their sources. While there are many sites that facilitate illegal activities, there are also legitimate sites that provide valuable resources, including educational materials and tools for privacy protection.
Financial Fraud Dark Web Statistics
Early participants may see some profit, but that money usually comes from new victims, not actual earnings. Eventually, the system collapses, and most people lose their entire investment. Purchases through links on our pages may yield affiliate revenue for us. We review and list tools and products without bias, regardless of potential commissions. This is an estimated reading time to let you know how long it will take you to read all the content on this particular PrivacySavvy.com page.
Finding Trusted Onion Sites
The resulting data set includes for each transaction the source and destination entities, the time, and the value of the transaction. This suggests that the multiseller activity is sensitive to external shocks but also that it yields higher profits. The number of multisellers steeply decreases after operation Bayonet but they still sustain high incomes. Nevertheless, by analysing the income of each multiseller, we observe that the median income still reflects their high income, as shown in Fig. Individually, they are able to yield significant high incomes compared to other types of sellers.