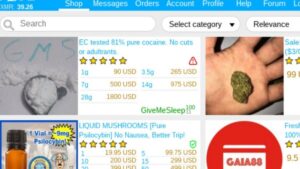
These marketplaces are full of risks (security, legal, ethical issues – all of them). But if you...
darknet
The dark web marketplaces are mainly defined into two categories. In the first arc of the anime...
Also, use an effective antivirus program to check threats if you decide to download files. You can...
In Afghanistan, there is a symbiotic relationship between narco-traffickers and the insurgency, as narcotics traffickers provide revenue...
The ability to seamlessly communicate with vendors via secure messaging systems also greatly improves overall user experience....
For 2025, they’re teasing AI-powered search—could make digging through listings a breeze, which I’m hyped for since...
MGM Grand darknet market gained popularity due to the closure or inaccessibility of other markets. It has...
While this market started in Canada in 2021, WeTheNorth now sells to both Canadian and international users....
One of Daniel’s impressive features was the built-in functionality that showed whether a particular dark website is...
Freshtools was established in 2019 and offers various stolen credentials, accounts, and host protocols like RDP. It...