The dark web combines encryption, anonymity, and hidden doorways to provide the perfect sanctuary for such illicit...
credit
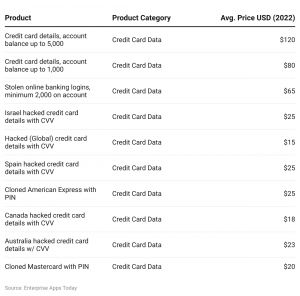
When a hacker writes up new malware, steals a database, or phishes someone for their credit card...
This type of payment uses tokenization, which replaces your sensitive card data — like the expiration date...
While this might seem like a dystopian nightmare, understanding the inner workings of these dark markets is...
Kivimäki and his friends enjoyed harassing and terrorizing others by “swatting” their homes — calling in fake...
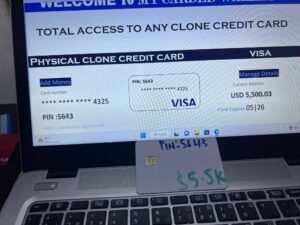
As a result, carding communities are developing new strategies to leverage existing online platforms and withdraw money...
With stolen payment cards, a cybercriminal can immediately make purchases under your name, or even drain your...
As you discover the hidden depths of the web, ensure your sensitive data remains protected, no matter...
Simultaneously, customers face the risks of identity theft, damaged credit scores, and the emotional toll of financial...
Engaging in illegal activities can lead to severe legal repercussions, including fines and imprisonment. Moreover, the financial...