However, these features can be used for both legitimate and malicious purposes. This is the primary reason...
Law enforcement conducted a search of his residence and vehicle, seizing electronics and cash. In addition to...
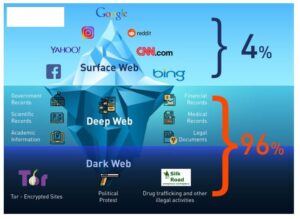
The market is accessible through the Tor network, which provides users with anonymity and security. It is...
This material is called child sexual abuse material (CSAM), once referred to as child pornography. It is...
Those who use these services can still be traced and prosecuted if caught, especially as law enforcement...
It is best known to western audiences for the annual No-Laughing Batsu Games and the original version...
This platform not only fosters a sense of community but also promotes sustainable practices among consumers and...
With ZeroBin, you can easily exchange encrypted messages within the dark web. With 256-bit AES encryption, this...
Without thorough pre-transplant evaluations, recipients face a higher risk of graft failure and additional procedures that jeopardize...
If you’re using a browser like Tor and visiting .onion websites that aren’t accessible through regular search...