
This darknet site sells US fake driver’s license for most states. These licenses are scannable, and have original hologram, UV, microprint, and laser engraving etc. In other words, it’s a watch-only version of Twitter which lets you follow (stalk) people anonymously, without having to sign up. Basically, use it if you simply need anonymous e-mails without a lot of guarantees or aren’t doing something that’s extremely illegal.

How Our Data Ends Up In Hidden Markets
As of 2020, nearly 57% of the dark web was estimated to contain illegal content, including violence and extremist platforms. Sometimes, you might be hacked by using weak passwords or even just connecting to unsecured Wi-Fi on public networks. And in a world where almost everything we do is online, taking your digital privacy seriously is more important than ever. First things first, always use strong and different passwords for each account you open. Too-good-to-be-true investment offers are another classic scam on the dark web.
We review and list tools and products without bias, regardless of potential commissions. AiPrise uses document verification, biometric checks, and data cross-referencing from over 800 sources to spot fake or manipulated identities. It helps businesses catch fraud early, meet compliance requirements, and streamline customer onboarding. Strong identity checks help you stop fraud before it starts. With the right tools, you can flag fake profiles, meet KYC requirements, and onboard customers without slowing things down.
Production Of Fake Documents
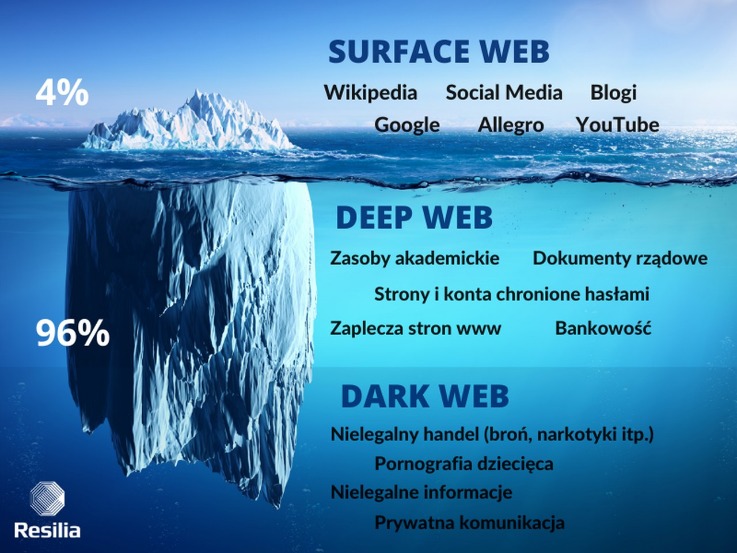
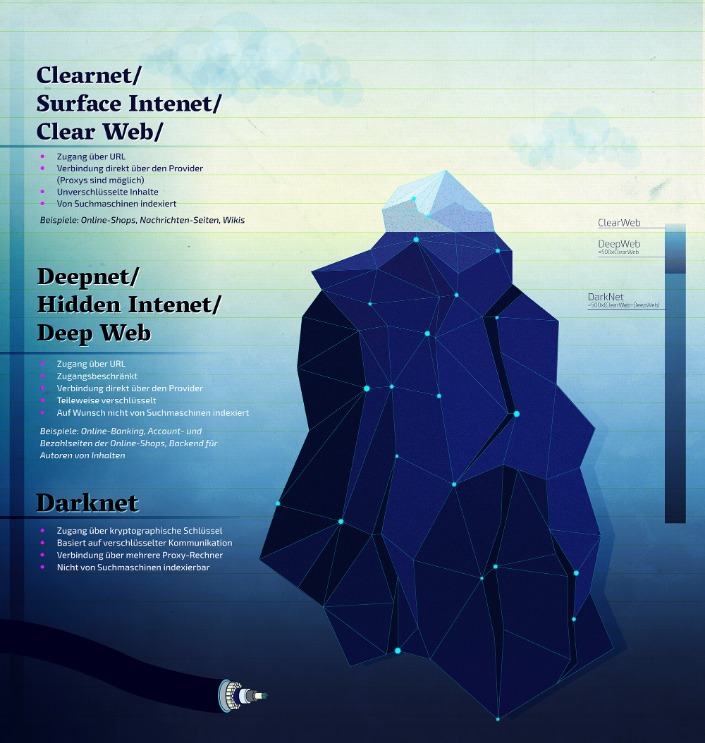
All that one can expect from a deep web marketplace when it comes to anonymity and security. Moreover, the layers of encryption and the bounce of your data from node to node effectively mask your IP address, enabling online anonymity. It allows access to the .onion sites on the dark web that you won’t find using a regular browser. Darknet markets operate within this hidden space, often hosting illegal activity, while the deep web primarily consists of everyday private or password-protected content. Even passive activity on these sites can contribute to criminal networks.
- If the operating system detects any non-anonymous connection, it blocks it, thus ensuring maximum online protection.
- If your order is not processed in 5 days, money will transferred to your BTC wallet automatically.
- As you are now familiar with the three different sections within the entire world wide web, let’s take a closer look at how you can access the dark web anonymously.
- Since 2020, 2easy has sold massive stealer logs with sensitive data like passwords, bank cards, and initial access credentials.
- Perpetrators threaten to publish sensitive information in order to extort ransom money.
Is It Illegal To Enter The Dark Web?
- One thing that distinguishes BidenCash on the dark web, however, is how it markets itself.
- Silk Road quickly grew into the largest darknet market, handling hundreds of millions in transactions.
- The increase in data breaches and data leaks has led to more personal data being available for trading on the darknet.
- These anonymous marketplaces—operating mainly on the Tor network—are now a primary threat vector for businesses and cybersecurity professionals.
It tracks changes to your credit report and helps you spot potential identity theft early, so you’re not the last to know when something goes wrong. Once your personal information hits the dark web, it’s nearly impossible to remove it. But while you can’t undo a data breach, you can take control of what happens next. From strengthening your digital habits to setting up fraud alerts and monitoring your accounts, small steps can make a big difference. One of the central76 discussion forums was Reddit’s /r/DarkNetMarkets/,777879 which has been the subject of legal investigation, as well as the Tor-based discussion forum, The Hub. 🔹 Protect Your Business with CyberNodAt CyberNod, we provide comprehensive Dark Web scanning and cybersecurity assessments to help businesses identify and mitigate risks.
Run Antivirus/Anti-Malware Software
Anyone can access the deep web by using specialized search engines, dedicated web directories, and other sources that can help you find the data or information. The deep web is made up of content that search engines such as Google do not index. Such data includes medical records, financial information, research papers, private forums and networks, and other content. High-profile takedowns and scams have shaped the current landscape. For example, AlphaBay Market – once the largest dark web marketplace – was seized by US and international law enforcement in 2017.
Microsoft Strengthens Security After China-Linked Attacks
ASAP is a tech nerd’s playground—accepting BTC, LTC, ZCash, and Monero, it’s got options for days. Their DeadDrop system’s a standout—vendors stash your goods IRL, no mailing hassles—and wallet-less payments mean no one’s bolting with your cash, a relief after I got burned once by a shady escrow dodge. Listings aren’t public, but it’s steady—think drugs (weed, pills, some synthetics), a few digital extras like cracked accounts. They’ve got 2FA and encryption that’s tighter than a drum, which I’ve tested against crash-prone sites and found solid. Word’s out they’re going decentralized in 2025—less downtime, more trust, right in line with where things are headed. The site’s slick—vendor stats update live, checkout’s a breeze, and the vibe’s modern without being over-the-top.

Ready To Explore Web Data At Scale?
The criminal networks on Telegram are often well organized. For example, there are specialized groups for different types of data leaks. Sellers present their offers in public channels, while transactions are mostly conducted in private chats or via automated bots. These bots facilitate trade by providing price lists, taking orders or even automatically responding to customer queries. Despite increasing criticism of Telegram’s role in cybercrime, the platform only takes limited action against illegal activities. Although channels are occasionally blocked, new groups are usually created within a few hours.
This handy feature monitors the dark web for signs that your login details or other personal info have been leaked. These days, dark web forum admins are stepping up their game. They’re tightening security and carefully screening anyone who wants to join.
This vetting process helps keep the community “clean” from spies, law enforcement, or anyone who might pose a risk. According to a recent trend, the dark marketplaces faced a decline in revenue. Chainanalysis, a blockchain analysis firm, conducted research that shows that the revenue decreased from $3.1 billion (2021) to $2 billion (2024). Like ransomware, criminals can buy software and inject your devices with viruses. With it, they can spy on people, steal their sensitive data, or secretly control their devices.
Feather – A Free Monero Desktop Wallet
Anything from planting malware and stealing sensitive files to hijacking email accounts or breaking into social media profiles. Some services even target entire companies or public systems. Next up is Abacus, another newer market that has already made a massive name for itself, especially following AlphaBay’s closure.
On the dark web, even a minor slip-up can cause you big consequences. So, you need to be extremely cautious because the fake sites are often very similar to the real ones, making them dangerously convincing. Surprisingly, most guns on the darknet actually start as legal products. The UNODC (United Nations Office on Drugs and Crime) maintains that almost all firearms are originally manufactured through legal means. The dark web is designed in such a manner that it hides the identities and locations of its visitors. This extra privacy makes it much harder for authorities to track down who runs these markets and where they are located.



