The use of the dark web raises suspicion as it shows there is something you want to do privately. Remember that illegal activities can still incriminate you, whether you are using a Tor browser. For example, you shouldn’t pirate copyrighted material, engage in terrorism, or share illegal pornography. The creators assert that because their technique is so strong, even malware with root access could not determine the machine’s IP address.
Essential Security Tips For Using Dark-Web Marketplaces
At first glance, Tor doesn’t look that different from your regular browser – it has a search bar, lots of quick-launch icons, the peeled onion icon smack in the middle of the screen. Well, now it’s time to fire up Tails and do a little bit of tinkering. Chill, because nobody will ever find a record of you ever fiddling around the darknet.
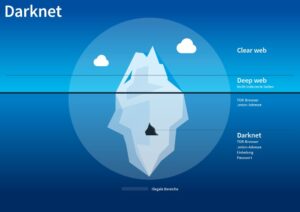
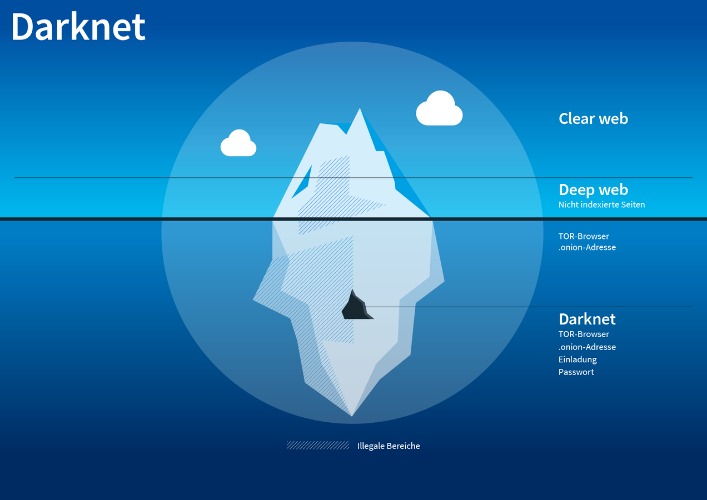
So, sites that contain a domain extension like .com, .org, .net, .biz, .info, etc. can be found on the surface web. In addition, the content on the pages don’t need any special or custom configuration to access. It might sound weird that Google doesn’t index these pages, but it does carry some logical sense. Google’s purpose is to show the most relevant information to all of its users quickly and easily.
Do Search Engines Like Torch Filter Content?
Keep in mind that you’ve to use very specific keywords when searching. And most importantly, be patient as you’ve to sort through a lot of useless results. These search engines work best if you already know what site you’re looking for, not for general browsing.

Tor Browser & Access
Alternatively, users can connect in opennet mode, which automatically assigns peers on the network. Unlike darknet mode, opennet uses a handful of centralized servers in addition to the decentralized peer-to-peer network. Obviously, finding these .onion websites is the first challenge, as they won’t show up in Google search results.

Hidden Answers
Having outlined the previous investigations and the significance of developing the new darknet drug markets research methodology, we now turn to the methods employed to investigate these issues. Studying illicit drug circulation and its effects on population health is complicated due to the criminalization of trade and consumption. Illicit drug markets have evolved with IT, moving digital to the “darknet.” Previous research has analyzed darknet market listings and customer reviews. Research tools include public health surveys and medical reports but lack neutral data on drugs’ spread and impact. This study fills this gap with an analysis of the volume of drugs traded on the darknet market.

How To Find New, Active Dark Web Links
This information can be used to target ads and monitor your internet usage. Also, there’s a vast amount of unsavory content on the dark web, as well as a significantly high number of hackers and scammers looming on the platform. That alone might already raise suspicion and place you under special surveillance. Some reports say the FBI will simply label you a “criminal” once they’re aware you’re using the Tor browser. It’s impossible to access the dark web with a regular browser like Chrome or Safari. That means that when Tor is compromised, or perhaps there’s a new vulnerability exploit in the Tor network, a VPN will still protect your privacy.
Emerging Darknet Marketplaces Of 2025 Anatomy Tactics & Trends
Torch is one of the oldest and most popular onion search engines on the dark web, serving over 80,000 requests per day. Torch is funded primarily through advertising—purchased in BTC, of course—which is why you’ll find the front page blanketed with old-school banner ads of dubious origins. Search engines on the dark web are a bit of a contradiction because dark web sites by definition are not indexed by traditional search engines. Your real information could be exposed at these nodes, allowing third parties to intercept your dark web activity. That’s why we recommend connecting to VPN before accessing Tor—VPN encryption protects your data, and changing your IP adds an extra layer of privacy to protect you.
- The provider also offers a dedicated CyberSec suite that prevents annoying ads and blocks malware and trackers.
- He was formerly the Chief Financial Officer and a principal shareholder of Apollo Solutions, Inc., which was acquired by CNET Networks.
- There’s also a search bar that you can use to search for any particular product or vendor.
- Kerberos has grown rapidly — some reports note over 1,100 listings within seven months, while others claim 5,000+ listings — showing a strong vendor presence.
They used “free data dumps” and emotional marketing to build trust before vanishing—an enduring lesson in the risks of social engineering. BriansClub remains a long-standing credit card data shop since at least 2014. Despite a 2019 breach that exposed over 26 million credit cards, it continues to operate, indicating sustained trust in its data pipelines. Darknet is your best source for the latest hacking tools, hacker news, cyber security best practices, ethical hacking & pen-testing. Learn how to automate financial risk reports using AI and news data with this guide for product managers, featuring tools from Webz.io and OpenAI. Freshtools was established in 2019 and offers various stolen credentials, accounts, and host protocols like RDP.
What Is Tails Software Used For?
Yes, DuckDuckGo has a .onion version that works through the Tor browser for anonymous searching. Unique in that it can be accessed via the clearnet (not just Tor). Useful for public threat research, though limited in index depth. Known for its massive index and premium version, Haystak is favored by cybersecurity professionals and threat analysts for its depth.
Most e-commerce providers offer some kind of escrow service that keeps customer funds on hold until the product has been delivered. However, in the event of a dispute don’t expect service with a smile. Every communication is encrypted, so even the simplest transaction requires a PGP key. Medical records, fee-based content, membership websites, and confidential corporate web pages are just a few examples of what makes up the deep web.
The mandatory barring of leaving houses for people during the COVID-19 disaster limited the supply of drugs in Russia. We do not have monthly data on drug poisoning, but we found significant correlations with this variable in yearly data. However, when it comes to darknet markets, the story is very different. Dark web marketplaces are mostly hubs for illicit goods and activities, posing serious risks to users and the wider community. Abacus Market is one of the newer darknet marketplaces that quickly filled the gap left by AlphaBay’s takedown. It hosts over 40,000 listings and offers everything from illicit goods and substances to hacking tools.