The US Supreme Court has indicated that even casual browsing could lead to legal consequences. Fill out the form to speak with our team about investigative professional services. How would you like to be able to export all your orders to a .csv file you could import into any shipping label software you liked? Automatically decrypt all the addresses and get your labels done in five minutes, even if there’s a hundred of them.
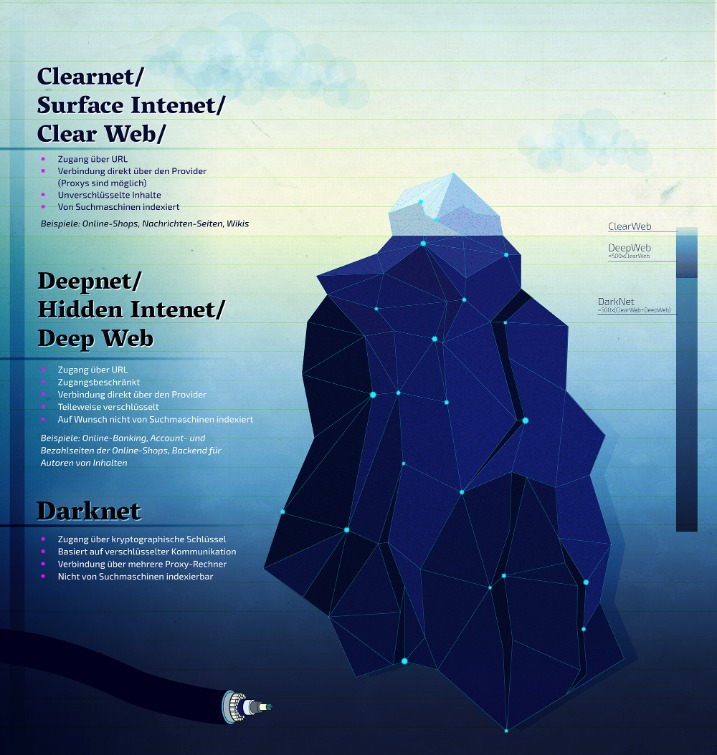
One of the key features of top-tier darknet markets is their use of Tor networks, which provide users with a high level of anonymity. By routing traffic through multiple nodes, Tor ensures that IP addresses are concealed, reducing the risk of exposure. Additionally, many markets now implement multi-signature escrow systems, which protect both parties by holding funds until the transaction is confirmed as successful. The market facilitates trades in stolen credit card data, hacked bank accounts, and services to facilitate the laundering of cryptocurrency. Therefore, you must know how to access dark web marketplaces safely (covered later in this article). In addition, know that while accessing the dark web is legal in most countries, engaging in illegal activities (buying or selling contraband, hacking services, etc.), is illegal everywhere.
Disgruntled Developer Gets Four-year Sentence For Revenge Attack On Employer’s Network
Even the smallest details about you can be useful to cybercriminals. That all is for general internet activities, you can guess how crucial having a VPN is when you hop onto something like the dark web. They’re tightening security and carefully screening anyone who wants to join. This vetting process helps keep the community “clean” from spies, law enforcement, or anyone who might pose a risk.
Roundup – Best VPNs For Speed
These products are often sourced from international suppliers, ensuring competitive pricing and a wide variety of options. Digital products, such as e-books, software, and online courses, also play a significant role in the ecosystem, catering to a diverse audience. The use of cryptocurrencies like Bitcoin and Monero remains central to the darknet ecosystem, providing anonymity and reducing the risk of financial tracking.
Silk Road (2011–
These sites provide a level of privacy and anonymity unavailable on the surface web, offering content and goods that cannot be easily found through traditional online platforms. The dark web is infamous for containing sites such as Silk Road and other marketplaces where users could potentially buy drugs and/or weapons, stolen credit cards, IDs, and much more. H25.io is a premium directory in the Tor network, offering access to a diverse and meticulously curated list of onion sites. Our mission is to simplify navigation in the complex and evolving world of the darknet. Here, you’ll find links to various resources, including educational archives, private forums, anonymous services, and more. Users must look for platforms employing robust encryption protocols, secure escrow services, and advanced anti-phishing measures.
Legitimate Use Cases For The Average User
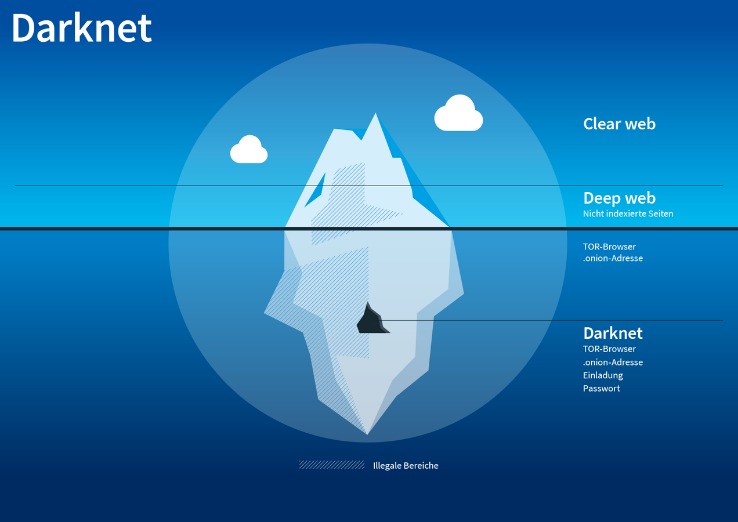
Buy login credentials to a $50,000 Bank of America account, counterfeit $20 bills, prepaid debit cards, or a “lifetime” Netflix premium account. The dark web is a part of the internet that isn’t indexed by search engines. You’ve no doubt heard talk of the “dark web” as a hotbed of criminal activity — and it is. Researchers Daniel Moore and Thomas Rid of King’s College in London classified the contents of 2,723 live dark web sites over a five-week period in 2015 and found that 57% host illicit material. No, black market websites operate illegally and pose high risks of scams, fraud, and law enforcement action. WeTheNorth is a Canadian market established in 2021 that also serves international users.
Today’s cybercriminals spread their activities across multiple platforms, making them harder to track and shut down. While this topic may seem distant for most people, understanding how these spaces operate is crucial. It helps us stay more vigilant, better protect ourselves, and make informed decisions online. For several years, Yahoo was at the apex as the internet’s best web service provider, offering…
Another Marketplace Doxxed: “HansaMarket”
As I mentioned previously, the dark web is quite popular with journalists, political bloggers and news publishers, and others who run the risk of imprisonment in countries like Iran and others. Supreme Court will allow the FBI to search and seize any computer that’s using the Tor browser or VPN. Rule No.41 allows a federal judge to issue a search and seize warrant for any person who is using anonymity software like Tor. Click on “Safest.” As you’ll see, JavaScript and a few other features will be automatically disabled on all sites.

How To Browse Anonymously On The Darknet Market?

You should also consider freezing your credit to prevent identity theft. You can use dark web monitoring tools, such as NordVPN’s Dark Web Monitor, to check if your data has been leaked. These tools scan dark web forums and marketplaces for any signs of your compromised credentials.

In fact, everything is in English, and the site picks up users everywhere in the world. People visit this market to buy stolen credit cards, personal data, remote desktop account credentials, and logs gathered from information-stealing malware. Brian’s Club has been around since 2014 and remains one of the most well-known credit card shops on the dark web. It sells stolen card data — dumps, CVVs, even wholesale batches — and lets users bid on fresh leaks. Despite multiple takedown efforts by law enforcement and security researchers, Brian’s Club has resurfaced repeatedly and continues to add new stolen credit card data. Abacus Market is one of the newer darknet marketplaces that quickly filled the gap left by AlphaBay’s takedown.
- Weapon Marketplaces – These marketplaces are designed for people who want to buy or sell weapons.
- In opennet mode, the network will automatically assign you to other users on Freenet’s network.
- Hypothetically speaking, Google may be aware of well over 200 trillion individual pages (these are obviously NOT all indexed in the search engine).
- Many “trusted” sellers use fake reviews or steal reputations from shutdown markets.
- Platforms known for consistently resolving issues and eliminating fraudulent vendors quickly gain credibility and user loyalty.
The CSO Guide To Top Security Conferences

Thus, use the best antivirus software that protects against these online threats. Moreover, the layers of encryption and the bounce of your data from node to node effectively mask your IP address, enabling online anonymity. It allows access to the .onion sites on the dark web that you won’t find using a regular browser. Hansa was known for its security-conscious design to protect the anonymity and security of its transactions.
There are a variety of private and encrypted email services, instructions for installing an anonymous operating system and advanced tips for the privacy-conscious. Most e-commerce providers offer some kind of escrow service that keeps customer funds on hold until the product has been delivered. However, in the event of a dispute don’t expect service with a smile. Every communication is encrypted, so even the simplest transaction requires a PGP key. Dark web commerce sites have the same features as any e-retail operation, including ratings/reviews, shopping carts and forums, but there are important differences. When both buyers and sellers are anonymous, the credibility of any ratings system is dubious.