Second, bibliometrics often focuses on measures such as the number of citations a paper receives, which may not accurately reflect the quality or impact of the research 87. Third, self-citation can affect bibliometrics, where authors cite their work to boost their metrics 88. Fourth, bibliometrics needs to consider the context in which research is conducted or how it is used or applied 89. This can limit the usefulness of bibliometric measures in understanding the true impact of research. Finally, the results of a bibliometric analysis can be influenced by the search terms used.
Immigration Enforcement
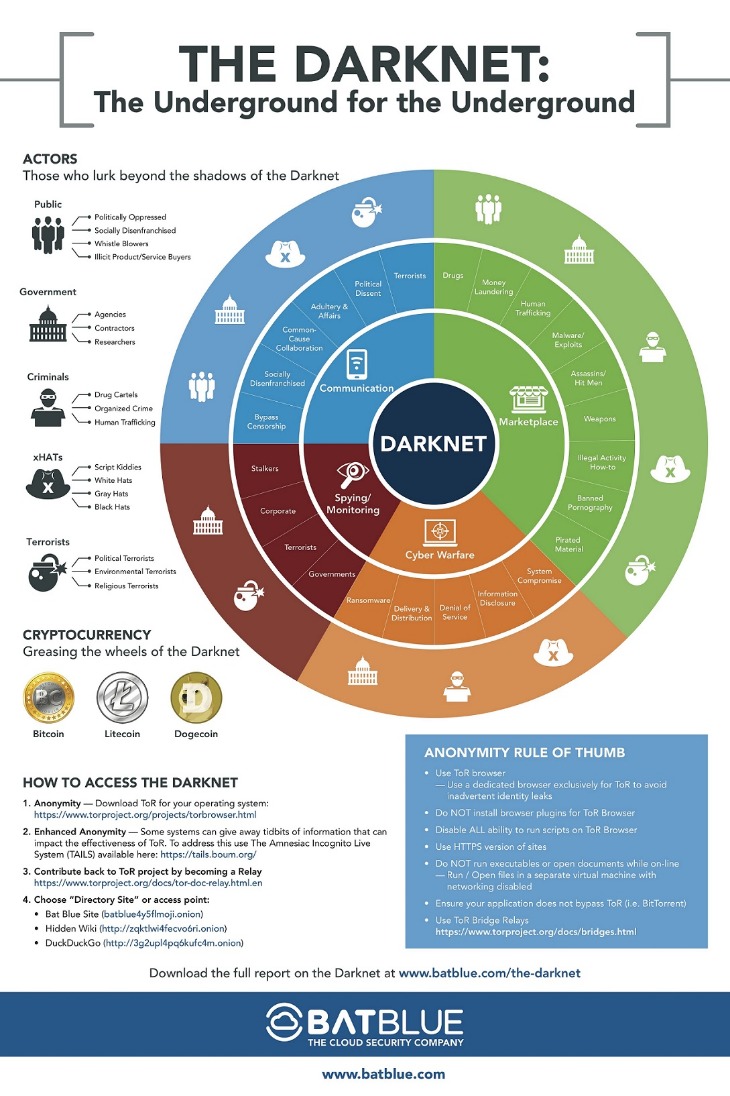
Another study 23 used the bibliometric method to analyze the trend of anonymous communication research between 2000 and 2022, using the Citespace tool to analyze authors, institutions, and journal collaborations. They highlighted “Darkweb” and “privacy protection” as keywords that could significantly influence future research. While many prior studies have demonstrated the popular use of the Darkweb for illegal services, a systematic literature review and bibliometric analysis of 49 papers in criminology and penology was carried out 24. Their study provides valuable insights into the evolution of Darknet-related crimes, including prolific authors, contributions from the Global South, and a need for balance in publications between regions.
Join Our Cyber World:
Inside, buyers could browse thousands of drug listings, many accompanied by reviews and ratings. The platform also featured prescription drug listings falsely marketed as authentic, and some products were outright scams—counterfeit pills advertised as legitimate pharmaceuticals. Two fentanyl precursors have also been assessed and recommended for international control by INCB, following a request made by the United States. The Precursors report also shows a surge in non-controlled fentanyl precursors in North America in 2023. Bibliometrics, or statistical analysis to measure the impact and importance of scholarly research, has several limitations. First, bibliometrics can be influenced by factors such as the prestige of the journals in which research is published, the language in which it is written, and the number of authors on a paper 86.
Officers recovered multiple pills in prescription bottles, packaging materials, gloves, black Ziploc bags and empty prescription pill bottles with the names of the defendants and other uncharged coconspirators. They used darknet markets, including Monopoly, Versus, ASAP, AlphaBay, Wall Street, Archetyp, Bohemia, Empire, Dream and White House. According to court documents, for six years, the married couple operated an online storefront called “MrsFeelGood” to illegally distribute a variety of narcotics across the United States.

Trump Ends Ex-Vice President Harris’ Secret Service Protection Early After Biden Had Extended It
This information can be useful for identifying opportunities for collaboration or for comparing the research funding landscape in different countries. Research on the Darknet will likely interest many countries and organizations due to the potential implications for cybercrime, national security, and internet governance. Governments, law enforcement agencies, and other organizations may, therefore, be interested in funding Darknet research to understand better and address these issues. Today, the Department of Justice, and its Joint Criminal Opioid and Darknet Enforcement (JCODE) team and international partners, announced the results of Operation SpecTor, which included 288 arrests – the most ever for any JCODE operation and nearly double that of the prior operation. Law enforcement also conducted more seizures than any prior operation, including 117 firearms, 850 kilograms of drugs that include 64 kilograms of fentanyl or fentanyl-laced narcotics, and $53.4 million in cash and virtual currencies.
Europol-coordinated Global Operation Takes Down Pro-Russian Cybercrime Network
He later pleaded guilty to narcotics conspiracy, money laundering, and conspiracy to sell adulterated and misbranded medications in the Southern District of New York. Designed to resemble a legitimate e-commerce platform, Incognito offered a slick user experience with branding, advertising, and customer support. Upon visiting the site via the Tor browser, users were greeted by a graphic interface and prompted to log in with a unique username and password.
Related Analysis
Since its inception in 2018, JCODE investigations have resulted in the arrest of more than 300 darknet drug traffickers, as well as the seizure of more than $42 million in drug-tainted proceeds, over 800 kilograms of narcotics, and approximately 145 firearms. Navia further admitted to supplying methamphetamine to Ta and Srinivasan’s drug trafficking operation. Some of the darker illicit goods and services able to flourish on the darknet due to its anonymity and privacy-centric nature include pornography, such as child sexual abuse material (CSAM), human trafficking, and the exploitation of humans both online and in the physical world. Criminals and traffickers have increasingly turned to the online cybersphere to exploit victims. Social media platforms can be used to identify possible victims, target them, recruit them, and then to advertise their exploitation services. The internet and darknet can be used to broadcast live acts of exploitation for distribution to a wider audience.
Others promise that they use the “best equipment” for the “highest stealth and security possible” – or reassure customers that they are experts in some other manner. As is typical on the darknet, many state that any listings of weapons for sale on Tor are scams. In other areas of the world, like Europe, there is more reliance on weapons purchases via the darknet; one underground marketplace advertised itself specifically as a provider of guns to the European Union. On average, DarkOwl analysts found that the prices of firearms for sale on the darknet were the same or lower than what the same products cost on surface web sites. However, in most cases darknet traded weapons were not significantly lower than prices advertised in the surface web. The group used stash houses in the San Fernando Valley to deliver the drugs hidden in stuffed animals.
Missing The Wider Landscape Of Digital Harms
- In the same period, 1,025 incidents involving parcels or couriers used for drug trafficking were also documented.
- District Court today to 135 months in prison for purchasing an opioid cutting agent from China.
- NLP techniques can analyze text-based content on the Darknet, such as online forum discussions or listings on Darknet marketplaces.
- This study examined the characteristics and behavior of a particular type of botnet and attempted to identify the motivations and tactics of the attackers behind it.
- JCODE is an FBI-led Department of Justice initiative, which supports, coordinates, and assists in de-confliction of investigations targeting for disruption and dismantlement of the online sale of illegal drugs, especially fentanyl and other opioids.
They also identify research gaps in Darknet technologies and find that Darknet projects are distributed in one-third of the global Internet. The authors find that computer worms and scanning activities are the most common threats investigated through the Darknet, but DDoS amplification and spoofing activities are understudied. While the telescopic view of Darknet activities is useful, a microscopic view of the Tor network’s hidden services was attempted 59. They developed a new dataset called “Darknet Usage Text Addresses” (DUTA) for studying Darknet active domains and the anonymous expression and illegal activity that occurs on the Deep Web. They built DUTA by sampling the Tor network and manually labeling each address into 26 classes. Using DUTA, they compared two text representation techniques and three supervised classifiers to categorize Tor hidden services.
Anderson pleaded guilty in June to conspiracy to distribute methamphetamine, one count of possession of heroin with the intent to distribute, and possession of a firearm in furtherance of a drug trafficking crime. The Darkweb is often used as a platform for distributing botnets and malware, which are tools that can be used for various malicious purposes, including distributed denial of service (DDoS) attacks, spamming, and identity theft. One example of recent research in this area is the analysis of a ‘/0′ stealth scan from a botnet 82. This study examined the characteristics and behavior of a particular type of botnet and attempted to identify the motivations and tactics of the attackers behind it. Other research has focused on identifying the most influential suspicious domains in the Tor network, a network of servers that can be used to access the Darkweb 83.
Hundreds Nabbed In Global Crackdown On Dark-web Drug Marketplace
Research on currency substitution in the shadow economy, which includes the Darkweb, has also examined the use of Bitcoin and other cryptocurrencies as an alternative to traditional fiat currencies 78. This research has used local Bitcoin trade volume as a proxy for adopting cryptocurrencies in the shadow economy and has found evidence of currency substitution in some cases. Research on the Darkweb, a secretive and often illicit part of the Internet, seems relevant to the UN SDG, particularly SDG 16 (Peace, Justice, and Strong Institutions).
Las Vegas Couple Sentenced To Prison For Drug Trafficking Through Darknet Market
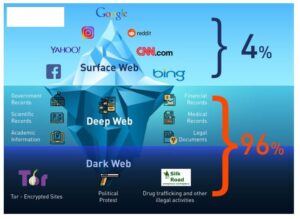
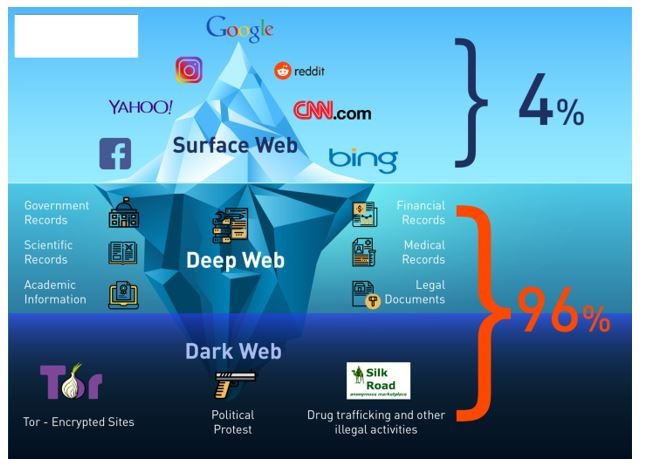
The use of the Darknet has become increasingly popular after the study 19 provided an overview of the Influence of the Darkweb in different spheres of society by discussing the number of daily anonymous users of the Darkweb (using Tor) in Kosovo and worldwide. Results are gathered from Ahmia and Onion City Darkweb’s search engines, and anonymity is also discussed. The paper calculates the number of users based on IP addresses and country codes and presents the number of users in anonymous networks on the Darkweb. As mentioned, anonymity through tools such as Tor causes the Darkweb to be a breeding ground for illegal activities such as pornography, weapon trafficking, drug trafficking, and terrorism. In a systematic literature review of 65 relevant articles from leading databases 20, the authors analyzed crimes, consequences, and methods to provide direction for cybersecurity researchers and specialists in identifying and addressing emerging crime threats on the Darkweb. The study found that further research is needed to identify criminals and crypto markets.