Monero’s my go-to for dark web payments because it’s darn near impossible to trace. With tricks like ring signatures and stealth addresses, it keeps your transactions off the radar—unlike Bitcoin, which can leave a trail if you’re not careful. Most markets, like Abacus or Archetyp, love it for that privacy kick. We The North Market is built for secure, trusted transactions with some of the lowest vendor fees in the industry.
Where To Find Darknet Market Links
Kerberos has grown rapidly — some reports note over 1,100 listings within seven months, while others claim 5,000+ listings — showing a strong vendor presence. User feedback on darknet forums is mostly positive, citing reliability and smooth transactions, though, as with all darknet markets, risks remain. The marketplace has an intuitive interface and offers powerful search tools that make it easy for you to find products from both local and international sellers. All vendors are vetted before they are allowed to sell, so it makes sure of trust and quality.
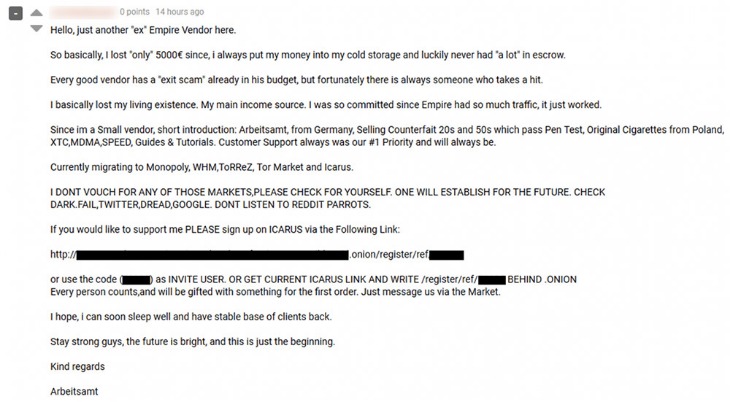
Exit Scams
Dark-web marketplaces attract sophisticated cybercriminals adept at launching phishing scams, malware attacks, or ransomware threats. Buyers and sellers frequently face risks from malicious actors posing as legitimate vendors or customers, potentially leading to financial loss or exposure of sensitive personal information. N 2025, dark web websites frequently change domains and are often short-lived. Accessing them may require .onion links and the Tor browser, but caution is advised due to legality and cybersecurity risks. No, black market websites operate illegally and pose high risks of scams, fraud, and law enforcement action.
The dark web is a hidden section of the internet that you cannot reach with common search engines like Bing or Google. The only way in is through the use of special software that renders all users anonymous and untraceable. Imagine an underground version of your favorite online marketplace, somewhere hidden, exclusive, and often operating outside legal boundaries. It is similar to an online store, except it’s not the type you’ll find with a quick Google search. These marketplaces are full of risks (security, legal, ethical issues – all of them).

But if you still decide to access these websites, for education or research purposes, make sure you stay cautious. Detailed stats on listings, trade volumes, and vendor counts across the top darknet markets. Today, in the post-Silk Road era, many online black markets continue to thrive.

What Is The Future Of The Deep Web Markets?
TorLinks maintains one of the most reliable directories of verified .onion sites. Its strength lies in regular updates and community-driven verification of links. I especially like how TorLinks categorizes links based on their type, letting you easily find what you need. SecureDrop is a really awesome Tor service that can be used to share information without revealing your identity.
How Did We Select These Best onion Sites?
This browser is the most suitable option for accessing the dark web, thanks to its multiple layers of encryption. Each time you connect to a dark web link, your request and traffic are routed through at least three different server points, ensuring your IP remains hidden. Naturally, this makes the dark web a breeding ground for illegal activity.

Which Markets Do Y’all Trust?
This directory lists only established markets with verified onion links. Despite its reputation, the dark web isn’t solely defined by illicit marketplaces or nefarious activity. Hidden networks also host a range of resources that can inform, educate, and support individuals who value anonymity. From uncensored libraries to secure whistleblowing channels, these platforms can offer benefits difficult to find on the clear web. Ensuring that the onion links you follow lead to the intended, trustworthy destinations can be a constant challenge on the dark web. The complexity and randomness of onion addresses make it easy for scammers and malicious actors to create spoofed versions of popular sites.
Ready To Explore Web Data At Scale?
It lets you search both clearnet and dark web sites, but it blocks all trackers, doesn’t use your location data, and never stores your search history. Whether for illegal pursuits or legitimate discussions on privacy and security, understanding the nature and function of these sites is essential for anyone curious about the darknet. The top darknet sites encompass a spectrum of services and communities, each with unique risks and rewards. Knowledge and caution are paramount when navigating this intricate space. In the first arc of the anime series Lupin the 3rd Part V, Lupin III steals digital currency from the “Marco Polo” darknet market. For a local machine configuration, he recommends a computer purchased for cash running Linux, using a local Tor transparent proxy.
II Security And Anonymity On The Dark Web
- Due to the privacy-forward ethos of the Tor project, Tor Metrics stresses that the data it collects must not undermine the anonymity or security of the network.
- Quality and validity of the data it provides justify its higher cost over other marketplaces.
- The extra connection layers can act as a significant burden to your browsing experience if you’re doing something that is bandwidth intensive.
- DigDeeper offers in-depth analysis of technology and privacy topics rarely covered by mainstream media.
- These tools scan dark web forums and marketplaces for any signs of your compromised credentials.
It’s also important to note that your activities on the dark web aren’t completely immune to web tracking, and the expectation of anonymity can create a false sense of security. You can run a dark web scan to see if any of your data has leaked onto the black market. And if you think you’ve fallen victim to identity theft or fraud, be sure to report the internet scam just like you would any other crime.
- We The North Market is built for secure, trusted transactions with some of the lowest vendor fees in the industry.
- But anything that’s against the law on the regular web or offline is also illegal on the dark web.
- Accessing them may require .onion links and the Tor browser, but caution is advised due to legality and cybersecurity risks.
- They suffer losses such as identity theft, financial loss, and emotional distress due to damage to their personal and professional lives.
- Basically, if a Tor IP leak occurs before you connect to the VPN, your real IP address will be exposed.
- We consider the things you ought to check before making your decision.
Is It Illegal To Visit Onion Sites?

Also, even in countries where accessing the dark web is legal, it’s still against the law to use or host sites that promote criminal activities. Keybase is a secure platform that lets people chat, share files, and collaborate — kind of like a privacy-first version of cloud storage service Dropbox or communication platform Slack. Everything you send through Keybase is end-to-end encrypted, which means only you and the person you’re talking to can see what’s being shared. Whether you’re sending personal photos, important documents, or just having a conversation, it all stays private and protected from prying eyes.
It is an archive stored on the Dark Web that keeps a snapshot of websites on the surface internet. The useful site allows you to see how a website looked at an earlier date. This lets you check what information it contained at a previous point in time. This onion site was created as a place for whistleblowers to pass information to journalists. It is a safe haven where anybody with information can share it anonymously and without fear of being tracked. You can use this community-edited link database to find everything from anonymous chat rooms, to Dark Web social networks, and blogs about various interesting subjects.
This traditional search engine is also compatible with the dark web and can help you find dark web websites. Anyone can archive or retrieve data on any site they want, wherever available. I personally recommend Tor over VPN because it’s the safer option — the VPN encrypts your traffic and changes your IP address, so the Tor network can’t see them. That’s helpful because Tor can suffer IP leaks and malicious actors can run Tor servers. Basically, if a Tor IP leak occurs before you connect to the VPN, your real IP address will be exposed.
New York Times
Although the Tor browser has sufficient encryption, combining it with a VPN offers better protection. However, you should not see it as an opportunity to engage in illegal activities to avoid trouble with authorities. This will help you to remain anonymous and secure at all Tor entry and exit nodes.



