As you discover the hidden depths of the web, ensure your sensitive data remains protected, no matter...
wpadmin
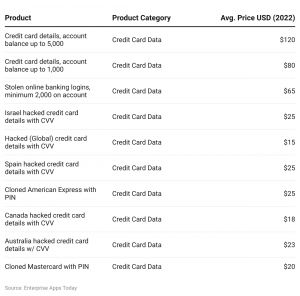
Simultaneously, customers face the risks of identity theft, damaged credit scores, and the emotional toll of financial...
In addition, mainstream search engines also track your searches and collect personal information. Don’t ever reveal your...
Law enforcers can use custom software to infiltrate the dark web and analyze activities. You could be...
Arnett said he consulted legal ethics experts before he passed a warning to federal prosecutors. Johnson had...
It is considered a go-to site for malware purchasing, providing keyloggers, trojans, and other Malware as a...
The market specializes in the sale of drugs, digital goods, and services, and is primarily aimed at...
This file contains additional information, probably added from the digital camera or scanner used to create or...
However, these features can be used for both legitimate and malicious purposes. This is the primary reason...
Law enforcement conducted a search of his residence and vehicle, seizing electronics and cash. In addition to...