This free, open-source browser routes your traffic through multiple volunteer-run servers, scrambling your data and making it very challenging for third parties to track you. As the dark web and the deep web constitute the hidden part of the internet, not every browser is compatible with taking you beyond the surface web. You can get it on the Hidden Wiki, Wikipedia for the hidden internet.
Tor Browser For Windows
You are not required to provide your personal information to create an account. The email service is available both on the surface and on the dark web. The goal of an anonymous and privacy network, Tor, is not to engage in the extensive collection of data.
Other Ways To Access Dark Web Platforms
The dark web browsers will help those who will bow before complete anonymity and security over the internet, especially when they are on the dark web. Tor anonymizes by bouncing traffic through relays; VPN encrypts and routes through a single server. While difficult, tracking is possible if security measures are misconfigured or if users reveal personal information. Check onion links through trusted directories, user reviews, and reputation checks. Tor encrypts your traffic and routes it through multiple volunteer-operated relays, making it difficult to trace. Use directories like The Hidden Wiki or Dark.fail, which list verified and regularly updated onion links.
“It’s a web browser. Use it like one. It’s that simple,” says Muffett. That’s the desktop edition, but there’s a version for Android and an unsupported onion browsing app for iOS. Uninstalling Tor Browser is as easy as deleting it and emptying your recycle bin. Some people get confused when trying to uninstall Tor, since it doesn’t show up in system programs. That’s because Tor is a fully portable, self-contained .exe file.
Step 4: Configure Basic Settings

Also, the final relay of the Tor network is not encrypted, meaning that traffic between the exit node and destination server could be monitored. Toorgle allows users to discover hidden websites on the Tor network without necessarily requiring the Tor dark web browser itself. Functioning as a proxy, the Toorgle search engine crawls “.onion” links and presents text-based content and torrent files directly through its own interface. Its “Tor Anonymous View” feature enables users to view content from dark web sites securely, masking IP addresses and preserving privacy without relying on JavaScript or tracking mechanisms. LibreY is a secure dark web search engine that prioritizes user privacy by operating without JavaScript. This is a significant feature, as JavaScript is often used to track web activity.
How To Access The Dark Web Safely
In fact, create new throwaway accounts and documents if possible. Ensure you have used prepaid and unidentifiable credit cards when purchasing on the dark web. Avoid using payment methods that can easily expose your identity.

Tor Browser’s Levels Of Security
These URLs are usually very long, consisting of a random jumble of letters and numbers. Though you likely won’t remember the addresses of onion websites, you can find these URLs on various websites on the internet. This guide will teach you how to install the Tor Browser in Windows easily so you can access the Dark Web or browse the web anonymously. The same general process applies to other operating systems, as Tor is also available for Mac and Linux. Unlike Tails, Whonix is built for everyday use and comes with all the major productivity apps, including a word processor and an email client.
Should I Use Services Like Web2Tor?

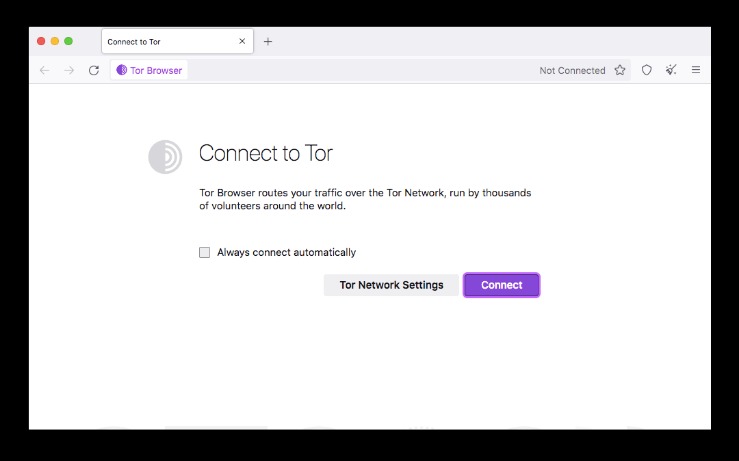
You will have to open the browser and connect it to the Tor entry node that further connects you to the Tor Network. You might wonder if Firefox being a regular browser, how will it be used for surfing the deep web links? You will be able to see it grouped with Safari, Google Chrome, Opera and more. The Tails come in a package of a variety of in-built applications such as an OS, an anonymizing browser, instant messaging service, office suite etc.
VPN Over Tor
- The Tor browser is a web browser that lets you access the Tor network.
- The “dark web,” in contrast, represents a deliberately concealed subset of the deep web.
- Whenever you type anything in a search engine on the clear web, say Google, it fetches the blogs, websites, videos, images, software, application and more.
- The main distinction, though, is that Tor takes a few moments to configure itself every time you launch it.
- Upon opening the Tor website, you will be presented with various download options for the operating systems that Tor supports, including Windows, macOS, Linux, and Android.
He takes a deep interest in Dark Web and thus spends most of his time knowing and writing about the nitty gritty of the Dark Web Market, Deep Web Links and Websites. Yes, Tor is slower due to multi-layer routing, but privacy is prioritized over speed. Secure communication for journalists, accessing privacy-focused forums, and whistleblower submissions. Live OS options that can be run on nearly any computer by simply popping a USB stick in and booting from it include Subgraph OS, Freepto, and Tails.
Some of these sites can be found through regular web browsers, but you’ll then need to switch over to Tor once you’ve got the onion links you want to follow. The Invisible Internet Project (I2P) Browser emphasizes a fully encrypted, decentralized approach to dark web access, routing traffic through an anonymous network of user-operated tunnels. It supports both web browsing and secure communication, offering additional services like email and instant messaging fully integrated into its secure environment. Choosing the right tools isn’t just about convenience—it’s a crucial step toward ensuring your personal safety, digital privacy, and anonymity. In this guide, we’ll explore the best browsers and essential tools available in 2025, empowering you to access the dark web responsibly, securely, and with confidence. If you need to use a computer and do not want to leave evidence behind (like a digital ghost), Tails is the best tool.

In 2004, the Naval Research Laboratory then released the code and made it open-source. Since then, volunteers and sponsors around the globe have maintained Tor and the Tor Browser. You are spoilt for choice with an extensive server network of over 7,600 in more than 118 countries.


The Tor Project offers Tor Browser for macOS, Windows, and Linux, as well as Android. From a macOS or Windows desktop, navigate via web browser to the Tor Browser download page and select the version for your operating system. From there, the Electronic Freedom Foundation maintains a thorough step-by-step guide for installing and using Tor Browser on macOS and Windows. The Tor Browser is a web browser that anonymizes your web traffic using the Tor network, making it easy to protect your identity online. While Tor may seem complex at first, it’s remarkably user-friendly. By following these guidelines, you can explore the power of privacy while browsing online.