The future of darknet markets is uncertain, but understanding the current landscape and emerging trends is crucial for anyone involved in or combating these underground economies. The top performers in darknet marketplaces for 2025, excelling in trade volume, vendor ratings, and market influence. We expect to see the number of attacks through contractors leading to data breaches at major end targets to continue to grow in 2025. Cloud platforms and IT services often store and process corporate data from multiple organizations, so a breach at just one company can open the door to many others. It is worth noting that a breach does not necessarily have to affect critical assets to be destructive.
Treasury Sanctions Head Of Online Darknet Marketplace Tied To Fentanyl Sales U S Department Of The Treasury

Bohemia maintains 22,000+ listings and $3M monthly BTC trades, with a 6% market foothold. Freshtools is a unique marketplace in that it does not only provide the stolen data, but it allows criminals to purchase MaaS which can cause further damage to the victims. It is one of the most active and up to date markets and always provides new and updated malware and data. It has built a reputation for being a reliable source of stolen credit card data and PII.
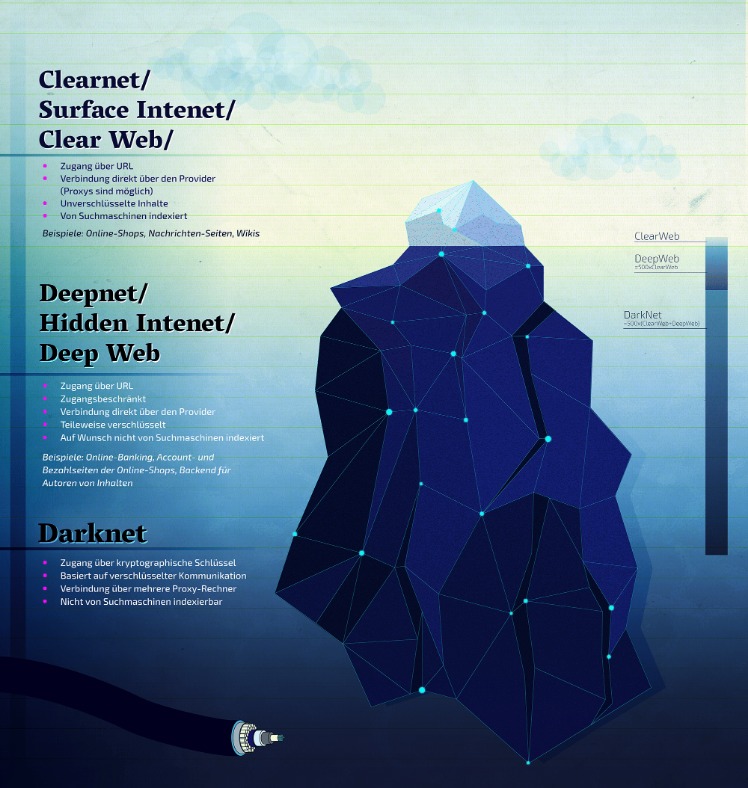
Introduction: How Much Of The Internet Can You See?
Following stricter bans on Telegram channels hosting cybercriminals, experts predict a resurgence of activity on dark web forums. Contrary to predictions, the market for cryptocurrency “cleaning” services, or Bitcoin mixers, stagnated. The competitive landscape remained unchanged, with no significant innovations reported.
Diverse Product Options On Darknet Platforms
- Only days later, the remaining marketplaces managed a total of $447,000 — a staggering 89.4% decline.
- In all, these marketplaces have recorded over 320,000 transactions, with more than 4,650 Bitcoin and 12,800 Monero — the go-to Dark Web cryptocurrency — transferred.
- Law enforcement agencies continuously improve their ability to trace transactions and monitor marketplace activity.
- Providers like Darktrace offer AI-driven security solutions that adapt to emerging threats, ensuring comprehensive protection across all endpoints.
- While stolen accounts across other categories saw year-over-year price drops, Deep Web facts reveal that crypto was up from 2022.
Without a single point of failure, decentralized markets prove far more difficult to shut down. Law enforcement cannot trace server IPs or arrest administrators because the markets have none. These systems use cryptographic access credentials, distributed file storage, and token-based payments to build fully autonomous criminal economies. These platforms run on peer-to-peer protocols without central servers or administrators. Smart contracts manage vendor-buyer interactions, and blockchain-based dispute systems replace traditional moderators. Abacus Market was launched in 2021 and now lists over 40,000 illicit goods, including hacking tools, counterfeit documents, and listings for drugs.

Payments are made with digital money, which helps protect the identity of both the buyer and the seller. This use of cryptocurrency makes transactions fast and secure, and it supports the overall goal of privacy on the dark web. While accessing Darknet Markets themselves is typically not against the law in most places, engaging with illicit goods within them is generally considered a crime. On the other hand, some people might visit Darknet Markets for lawful purposes such as research, journalistic work, or simply to explore online communities. It’s essential to know the local laws regarding online activities, and be cautious when using these platforms to avoid any potential issues. Given the global nature of darknet markets, international cooperation has become indispensable.
By routing internet traffic through multiple layers of encryption, Tor masks IP addresses, making it nearly impossible to trace transactions back to individuals. Nexus Market is known for its user-friendly interface and robust escrow system, which protects buyers and sellers during transactions. The platform supports a wide range of products, from digital goods to physical items, and employs a feedback system that enhances trust among users.
What Do People Sell Or Exchange On Darknet Markets?
Additionally, Tor enables users to access darknet sites hosted on .onion domains, something most common browsers can’t do. Since these markets operate on the Tor network, they require .onion links that are not indexed by regular search engines. Meanwhile, the proliferation of artificial intelligence (AI) is influencing the evolution of fraud. Criminals can use deepfake technology to impersonate individuals, bypass facial recognition checks, or carry out social engineering attacks. They may also automate hacking attempts using machine learning algorithms that adapt more quickly to security patches and defensive measures. This fusion of AI with illicit marketplaces could open the door to new forms of large-scale fraud, intensifying the cat-and-mouse game between cybercriminals and law enforcement.
Quick Links
It scans darknet marketplaces and hacker forums to alert you instantly if anything shows up. This way, you can catch any leaks and stop them before they cause bigger problems. The buyers, or “consumers,” are cybercriminals who use these tools to launch illegal activities. The victims, who are common users, businesses, and even banks, who end up paying the price. If you take a quick look through darknet marketplaces, you’ll instantly notice an overwhelming supply of pirated content.
US And Five Global Partners Release First Unified OT Security Taxonomy
When navigating darknet markets, users rely on updated market lists and verified links to avoid scams and phishing attempts. Platforms like Nexus Market and Abacus Market provide intuitive interfaces, making it easier for users to browse products and complete transactions. These markets often feature user reviews and vendor ratings, which help buyers make informed decisions. Dark Matter also runs an in-platform “Academy” with tutorials on PGP encryption, Monero use, and multisig transactions, catering to both newcomers and experienced darknet users. It features an experience-level system where users earn points for successful transactions, unlocking perks like personalized onion links.
Ransomware & Malware Ties To The Dark Web
JCODE and Europol’s European Cybercrime Centre (EC3) continue to compile intelligence packages to identify entities of interest. Parsarad was also indicted by a federal grand jury in the Northern District of Ohio on drug trafficking charges related to the illegal business he ran on the dark web. Another contributing factor is the encrypted communication and secure payment systems employed by these platforms.
Between January 2019 and September 2023, the majority of those queries came from underdeveloped countries with well-documented instances of internet censorship. Pakistan topped the list with 100 index points (maximum), followed by Kenya (89 points) and Myanmar (87 points). The top 10 also included Bangladesh (78), Ethiopia (75), Nepal (75), Cameroon (67), Tanzania (66), Nigeria (65), and Sri Lanka (63 index points). The surface web contains information that is easily available on the internet, and we are able to access it by surfing the internet, for example, YouTube, Wikipedia, Facebook, Google, blogs, and much more. According to Statista, the following digital products are being sold, with their average price in US dollars. The dark web, on the other hand, is a small part of the deep web that requires special tools like the Tor browser to access.
- According to a report by the International Telecommunication Union (ITU), IoT vulnerabilities are expected to triple by 2025.
- ASAP Market delivers 25,000+ listings with a 7% share and $4M monthly turnover, supporting BTC, XMR, LTC, and USDT.
- The combination of technological advancements and user-centric design positions these markets as a reliable and secure option for drug trade in 2025.
- Ares also uses sophisticated escrow protocols with optional multi-signature setups, offering a degree of protection in high-stakes transactions.
- Abacus Market appeared on the scene in 2021 and quickly became one of the heavyweights among English-speaking markets on the dark web.
- While not always mandatory, many regulations (e.g., GDPR, CPRA, HIPAA) encourage or require proactive breach detection, which includes dark web monitoring for exposed credentials or PII.
Some fake sellers take your crypto and never ship what you ordered, or phishing sites that look like real marketplaces but steal your login info. And then there’s malware—click the wrong link or download the wrong file, and your device could get infected. Stopping their growth takes serious effort from US agencies like the FBI, often working hand-in-hand with international law enforcement. From there, these products are then passed on to distributors, which are the dark web marketplaces in this context.

Signalling strategies in darknet markets often involve vendors and buyers establishing trust to facilitate transactions amid high risks. Opportunistic behaviors, on the other hand, involve exploiting weaknesses in market mechanisms—such as taking advantage of law enforcement takedowns or fake reputations—to maximize short-term gains. These behaviors are especially prominent in the context of darknet markets 2025, where the landscape continues to shift rapidly due to technological advancements and regulatory pressures.
Cybercriminals go on dark web marketplaces to buy and sell illicit goods and services. They engage in financial crime and sell other people’s stolen personal information, since they’re under the veil of anonymity. The anonymity and lack of rules that define darknet marketplaces are exactly what make them breeding grounds for fraudulent activities. Of course, the promise of secrecy and unfiltered access might lure you in, but those same features are what make the environment so risky.

Established in 2022, WizardShop is one of the biggest data stores on the dark web, focusing mainly on carding and financial data. Darknet is your best source for the latest hacking tools, hacker news, cyber security best practices, ethical hacking & pen-testing. Ignoring dark web activity leaves organizations blind to critical signals that often precede full-scale attacks. 🧠 Advanced groups may use PQC to harden ransomware C2s, malware encryption layers, and exfil pipelines.