Darknets and dark markets have fueled the growth of cybercrime, provided a marketplace for cyber threats, and expanded the attack surface for malicious actors. For directed betweenness centrality, paths must follow the direction of the edges, while undirected betweenness can follow edges in either direction. Like for harmonic closeness centrality, the weighted variants use the inverse of the edge weights during shortest path computation, such that stronger connections equate to shorter distances. As direction and weighting can have a large impact on the probability of lying on a shortest path, we use the directed weighted betweenness in this study.
Similar Content Being Viewed By Others
All communications are encrypted using PGP keys, and payments are processed through anonymous cryptocurrency wallets. The increased use of DeFi comes amid tight regulations on centralized exchanges. With stricter Know Your Customer (KYC) and Anti-Money Laundering (AML) measures, illicit actors are facing greater challenges when attempting to cash out. Furthermore, law enforcement worldwide has stepped up its efforts, seized assets, and disrupted key money laundering networks. Dark markets include features similar to those found in legitimate e-commerce platforms, such as product listings, user reviews, ratings, and customer support.
- Many darknet sellers post images of stolen documents or screenshots of leaked databases.
- Traditional methods of monitoring these hidden marketplaces are ineffective due to the anonymity and encryption used by darknet users.
- This interpretation would not be dissimilar to that of the ‘friendship’ relation in a social media network such as Facebook.
- It is not only used to display the identity in the market, but also is part of the account security mechanism.
- In many countries, strict laws limit who can legally buy, own, or carry firearms.
- Figure 2a shows that for all measures the currently most successful vendors have on average higher network centralities and activity indicators.
Explore Real-Time Projects In Cyber Security Summer Training For Hands
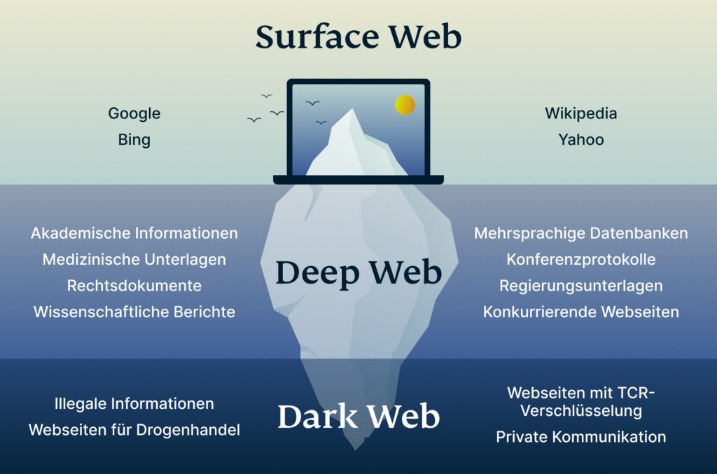
These sites often look basic or outdated, and their URLs are lengthy strings of random letters and numbers. Keep in mind that visiting the dark web isn’t illegal, but engaging in criminal activity there is. And, of course, think twice before sharing too much personal details online.
- In particular, we highlight that the twelve dark web markets we observed have different levels of security to protect themselves and their users.
- Stopping their growth takes serious effort from US agencies like the FBI, often working hand-in-hand with international law enforcement.
- Businesses should be aware of the potential for data leaks and invest in data loss prevention measures.
- You risk legal consequences if caught participating in illegal transactions.
- By being vigilant and advocating for stronger healthcare regulations and public safety measures, we can create a safer environment for everyone involved.
Primary Risks For Users Of Darknet Marketplaces
Therefore, users have the same opportunity to check whether their nickname is showing correctly after logging in. BidenCash and other exit-scam markets such as Torzon and Kingdom Market collapsed between 2022 and 2024. They used “free data dumps” and emotional marketing to build trust before vanishing—an enduring lesson in the risks of social engineering. Russian Market has operated since 2019, specialising in stolen credentials, stealer logs, and remote desktop access.
Ensure Tor Is Running (`torexe` In Background)
Moreover, a better and more detailed understanding of how rate limiting works may greatly improve the efficiency of crawlers and reduce manual labour. There are promising signs that we will soon be able to use a collection of scripts that can universally solve the kind of CAPTCHAs encountered in dark markets, which will be a very useful breakthrough. It is envisaged that machine learning techniques can be used to solve them quite easily in the near future.
Listen To This Post
The site is laser focused on drugs — that is the only product offered, whereas other marketplaces offer things like stolen credit cards and fake passports. In the interview, the admin claims that a certain substance turned his life around, and that he now believes drugs should be legalized, which is why he made the site. AI provides real-time insights, tracks illegal transactions, identifies cybercriminal patterns, and assists in digital forensic investigations. As cyber threats become more sophisticated, AI will play an essential role in detecting stolen data, preventing cybercrime, and protecting digital assets across the world.
Exploring The Use Cases Of Darknets & Dark Markets
These tasks might be further complicated when encryption is used for message contents. Specifically, the topic engagement indicator and betweenness centrality showed the best performance. First, this study focused on a single, somewhat older, dark web cryptomarket.

To reduce the workload for law enforcement, it can be beneficial to reduce the set of users that need to be manually investigated. Additionally, results showed that the vast majority (up to 98%) of post activity of the most successful vendors was produced by those included and that they were the relatively more successful vendors. As such, most successful vendors that are not retained by these measures are simply not very active on the forum. We note that the network centrality measures appear to require the communication network to have sufficiently developed and stabilised for good predictive performance. We found that betweenness centrality was the only network measure that was able to detect a substantial set of successful vendors that were not found by any of the activity indicators. High betweenness vendors may, for example, be connecting buyers of distant locations and/or diverse goods.
Significant technological innovations and trends have reshaped dark-web marketplaces over recent years. In 2025, many platforms have adopted decentralized architectures, reducing single points of failure that previously made them vulnerable to law enforcement takedowns. Despite Telegram’s anonymity, the dark web is still a hot spot for illegal trading of malware, illicit goods, and stolen data (such as stolen credit card information).

This time, they partnered with NordStellar analytics, whose researchers analyzed the largest dark web forums to uncover the most discussed and emerging topics. From advanced disinformation services to stolen digital identities, smart home vulnerabilities, and AI-driven social engineering — these are some of the key topics currently being discussed in dark web forums. “Europol has been compiling intelligence packages based on troves of evidence provided by German authorities, who successfully seized the marketplace’s criminal infrastructure in December 2021,” reads Europol’s public notice.
We are only able to cover the end-user side of security mechanisms, which may not be comprehensive. But we also raise ethical considerations for academics on how to properly and ethically improve research in this area. From the perspective of dark web users and vendors, there are almost no security mechanisms to prevent or mitigate such events because the operators are the ones who implement those mechanisms. The rich security mechanisms implemented actually attract users and vendors to join.
However, it is important to remember that these findings are about the average case; perfect delineations cannot be made. Even so, they indicate that the rankings induced by the measures have predictive potential for vendor success and may be useful to law enforcement activities. Figure 1 shows that, for all measures, vendors have higher network centralities and activity indicators than non-vendors. This indicates that betweenness has relatively small values overall with some extremely high outliers. On the contrary, harmonic closeness centrality has low relative difference scores but nominal absolute difference scores.