Immediately change your passwords, enable two-factor authentication, and notify your bank or credit card provider if the leaked information includes your financial data. If you’re using a browser like Tor and visiting .onion websites that aren’t accessible through regular search engines or browsers, you’re likely on the dark web. These sites often look basic or outdated, and their URLs are lengthy strings of random letters and numbers.
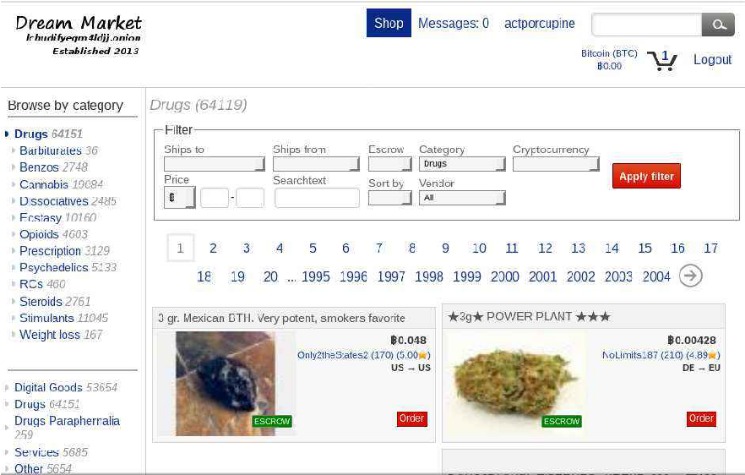
- It is similar to an online store, except it’s not the type you’ll find with a quick Google search.
- Hacked and verified Wirex and N26 accounts commanded the highest prices — $2,300 and $2,650, respectively.
- According to a recent trend, the dark marketplaces faced a decline in revenue.
- While Mega’s inflows declined by more than 50% year-over-year (YoY), Kraken DNM’s rose nearly 68% YoY.
- Disputes are low (2%), resolved in 36 hours for 90% of cases, backed by a 95% escrow success rate.
- Catering mainly to a Scandinavian customer base, it lists a large selection of narcotics, counterfeit currency, and hacking tools.
Largest Dark Web Marketplaces By Share
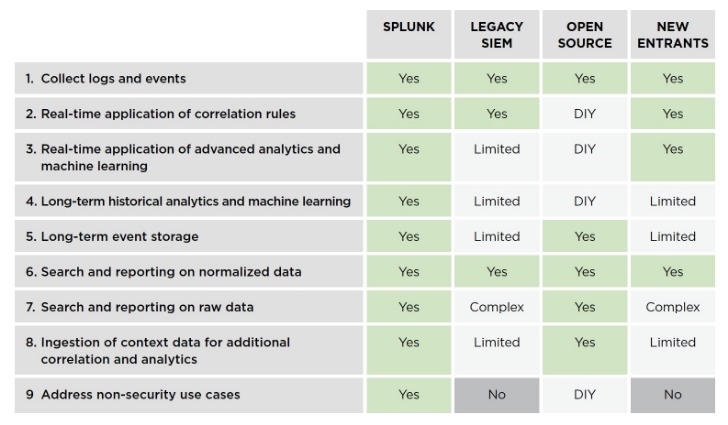
As cryptors, loaders, and stealers become more sophisticated, and underground markets remain resilient, organizations must prioritize robust cybersecurity measures in 2025. This shift will likely drive forum operators to introduce features like automated escrow services and enhanced anonymity to attract users. The number of malicious tools, or “drainers,” designed to steal cryptocurrency assets like tokens and NFTs saw a substantial rise.
Financial Institutions
However, you can trace its roots to the development of technologies like the Tor network or Freenet. In March 2000, an Irish grad student named Ian Clarke created the software application, Freenet. This was the initial framework for anonymous communication and file sharing. Later in 2022, the US Naval Research Laboratory built on Freenet’s idea to create a secure and encrypted network for sensitive communications, which was later released to the public as open-source software. As Telegram has end-to-end encryption and anonymous profiles, it makes it an ideal choice for threat actors and hackers to take advantage of. Like ransomware, criminals can buy software and inject your devices with viruses.
Darknet Market Vendors Evolve Their On-chain Behavior
Cybercriminals exchange large troves of compromised login credentials, financial information, and personal identifiers, fueling subsequent attacks like phishing campaigns and account takeovers. By giving malicious actors direct access to sensitive records, these data-focused marketplaces significantly expand the scope and impact of identity-based crimes. Supporting BTC (60%) and XMR (40%), Torrez’s interface offers advanced filters and fast trades—90% complete within minutes—keeping prices 5–10% below premium markets. Vendors like “TorrezRx” and “HackElite” boast 98% ratings, with 94% shipping reliability. Launched in 2021, Torrez surged post-Hydra, growing vendors by 200+ in 2025, and survived a 2024 DDoS attack with enhanced defenses. Its top-tier rank reflects its vendor scale and trade strength, despite slight uptime and turnover challenges.
Healthcare Services Group Data Breach Impacts 624,000 Individuals After 2024 Network Intrusion
The US and Europe have seen an increase in nitazine-related overdose deaths in recent years, perhaps due to the halt in the heroin supply following the Taliban’s crackdown. Due to the novelty of these substances (and the fact that many are analogs) the true number of overdoses in Europe could be higher, as forensic drug testing may lag behind the pace of the crisis. China-based precursor manufacturers mark the beginning of the synthetic drug supply chain. In years past, these organizations were more overt in their display of such products, openly advertising on mainstream B2B websites. Depending on the severity of the chemical, some manufacturers still follow this practice.
Rise Of Malware-as-a-Service (MaaS)
Market takedowns create temporary disruptions, but they rarely dismantle entire networks. Sophisticated players shift operations, adopt new aliases, and resume business within weeks. Farwa is an experienced InfoSec writer and cybersecurity journalist skilled in writing articles related to cybersecurity, AI, DevOps, Big Data, Cloud security, VPNs, IAM, and Cloud Computing. Also a contributor on Tripwire.com, Infosecurity Magazine, Security Boulevard, DevOps.com, and CPO Magazine. Changing the Tor browser settings can further boost your security levels on the dark web shops. For instance, you can choose the preferred security levels for enhanced protection.
China-based Vendors And Novel Synthetic Opioids
Some of the most profitable are now running openly on Telegram, including the one that researchers say is the biggest of all time. The Tor project gained notoriety for enabling illegal marketplaces like the Silk Road, a black market taken down by the FBI in 2013—and countless cybercriminal service providers ever since. Still, the Tor dark web browser also remains a vital tool for privacy-conscious users. The Tor browser, short for The Onion Router, is software that allows users to access the Tor network. Navy, it anonymizes Internet activity by routing data through multiple servers, masking your IP address. With cryptocurrency prices fluctuating, crypto-laundering gangs can capitalize on market volatility to conceal illicit funds, and use botnets to illegally mine cryptocurrency data.
Its design is clean and simple, built for pharma with filters by drug type, dosage, and seller rating (averaging 4.6/5 from 25,000+ reviews), making it an easy starting point for niche traders. The services were designed to help cybercriminals hide their crypto transactions and required little to no personal details for users to sign up, the Justice Department reported. Blender was once used by North Korea to launder stolen virtual currency, the DOJ claimed. Called Huione Guarantee, it provides scammers with personal data and tools to perpetrate their frauds. “With transactions totaling at least $24 billion, it is the largest illicit online marketplace to have ever operated,” cryptocurrency tracker Elliptic wrote in a report today.

AlphaBay’s back from 2021, run by DeSnake, and it’s still got that old-school cred despite just 330+ listings. They’re strict—no fentanyl or ransomware—which suits folks who like cleaner trades, a nod to the decentralized shift. BTC and Monero work here, with multi-signature wallets keeping things tight.
- In addition to various benzodiazepines, stimulants, and psychedelics, one longstanding China-based research chemical manufacturer also sells nitazenes.
- They’ve got a neat trick with a built-in Bitcoin mixer, plus Monero, so your payments stay hidden—perfect if you’re following our Monero tips.
- Operating since 2014, Brian’s Club is a long-running marketplace devoted to stolen credit card information, including dumps and CVVs.
- There are many regions in the world where governments change rules about the internet based on their politics.
- This is why activists and journalistic sources usually share sensitive information with investigative journalists through this platform.
This section explores the key trends shaping our top 10 darknet rankings as of February 27, 2025, offering insights into the forces redefining onion marketplaces, crypto trading platforms, and dark pool trading hubs. Whether it’s Incognito’s mandatory 2FA, Abacus’s advanced encryption, or Alphabay’s multi-layered DDoS protection, these platforms balance security with usability. Bohemia’s 850+ vendors maintain its 22,000+ listings, rated 4.4/5 across 30,000+ reviews, with drugs (70%), digital goods (20%), and fraud tools (10%) as key offerings. Response times average 16 hours, with a 92% shipping reliability rate—disputes occur in 3% of transactions, resolved in 48 hours for 85% of cases, supported by a 92% escrow success rate. Vendors like “BohemianRx” and “DataVault” offer 96% reliability, though its BTC-only focus and smaller pool keep it behind multi-crypto markets like ASAP. Alphabay’s 3,000+ vendors—the largest in our rankings—drive its 60,000+ listings, rated 4.9/5 across 100,000+ reviews.
Since 2020, 2easy has sold massive stealer logs with sensitive data like passwords, bank cards, and initial access credentials. It supports operations in multiple languages and operates on both clearnet and Tor. If you want more peace of mind, NordVPN has a dark web monitoring tool you can consider using.
Incognito Market added two-factor authentication to strengthen privacy across its 20,000+ listings. Kaspersky DFI researchers observed more than 11 hacktivist movements and various actors across the region. Both stealers and drainers are likely to be increasingly promoted as services on the dark web.